
Report to Congressional Committees
United States General Accountin
g
Office
GAO
June 2003
INFORMATION
TECHNOLOGY
Homeland Security
Needs to Improve
Entry Exit System
Expenditure Planning
GAO-03-563

Procurement s
INS’s initial expenditure plan and associated system acquisition
documentation and plans for the entry exit system partially meet the
legislative conditions imposed by the Congress. That is, INS has
implemented or has defined plans for implementing most of the legislatively
mandated requirements for the plan’s content, which include such areas as
capital planning and investment control, acquisition, and systems acquisition
management. However, key issues related to understanding and
implementing system requirements, such as developing a system security
p
lan and assessing system impact on the privacy of individuals, remain to be
addressed. Moreover, INS reported that it had obligated some entry exit
funding before it submitted the plan to the Appropriations Committees.
Since then, INS officials told GAO that they have de-obligated and
reclassified these obligations to other available funding sources.
GAO observed that INS has preliminary plans showing that it intends to
acquire and deploy a system that has functional and performance
capabilities that satisfy the general scope of capabilities required under
v
arious laws. These include the capability to (1) collect and match alien
arrival and departure data electronically; (2) be accessible to the border
management community (including consular officers, federal inspection
agents, and law enforcement and intelligence agencies responsible for
identifying and investigating foreign nationals); and (3) support machine-
readable, tamper-resistant documents with biometric identifiers at ports of
entry. Each of these capabilities is integral to supporting our nation’s border
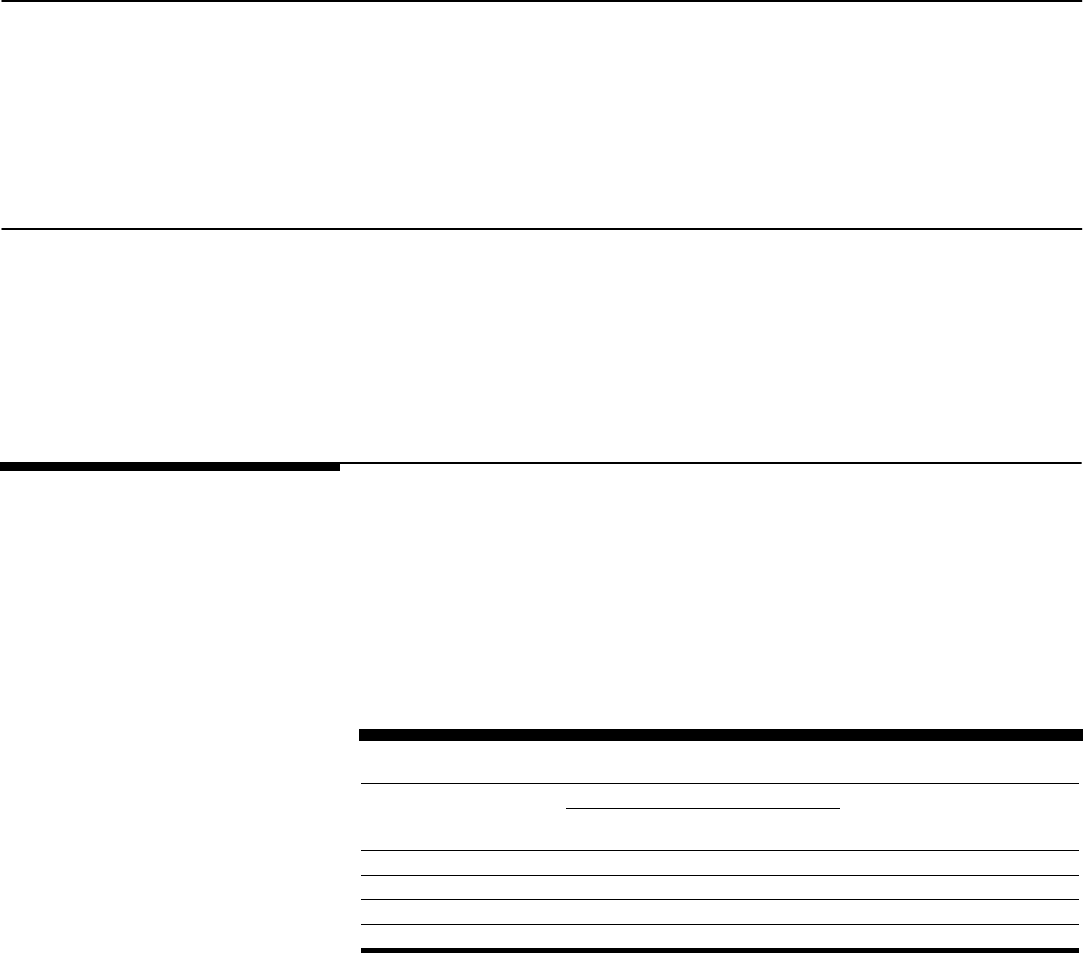
security process (see figure).
However, GAO also observed that the initial plan does not provide sufficient
information about INS commitments for the system, such as what specific
system capabilities and benefits will be delivered, by when, and at what cost,
and how INS intends to manage the acquisition to provide reasonable
assurance that it will meet these commitments. Without sufficiently detailed
information on system plans and progress, the Congress will be impeded in
its efforts to oversee the system.
Simplified Diagram of the Border Security Process
INFORMATION TECHNOLOGY
Highlights of GAO-03-563, a report to the
Senate and House Subcommittees on
Homeland Security, Committees on
Appropriations
www.gao.gov/cgi-bin/getrpt?GAO-03-563.
To view the full report, including the scope
and methodology, click on the link above.
For more information, contact Randolph C.
Hite at (202) 512-3439 or [email protected].
June 2003
Homeland Security Needs to Improve
Entry Exit System Expenditure Planning
Pursuant to legislative direction,
the Immigration and Naturalization
Service (INS), now part of the
Department of Homeland Security,
plans to acquire and deploy an
entry exit system to assist in
monitoring the flow of foreign
nationals in and out of the United
States. By separate legislative
direction, INS must submit to the
Senate and House Committees on
Appropriations a plan for this
system that meets certain
conditions, including being
reviewed by GAO, before funds can
be obligated. This report satisfies
GAO’s mandated review obligation
by (1) addressing whether the plan
submitted by INS, along with
related INS documentation and
plans, meets required conditions
and (2) providing observations
about the plan and INS’s
management of the system.
GAO recommends that the
Secretary of Homeland Security
(1) plan for and implement system
investment and acquisition
management controls and
(2) ensure that future expenditure
plans provide sufficient details to
permit an understanding of
(a) system capabilities, benefits,
cost, and delivery date and (b) how
the acquisition will be managed to
meet these commitments. The
department did not explicitly agree
or disagree with GAO’s conclusions
and recommendations, but
described actions it plans to take
that are consistent with these
recommendations.

Page i GAO-03-563 Entry Exit System Expenditure Planning
Letter 1
Results in Brief 2
Background 5
Fiscal Year 2002 Expenditure Plan Partially Satisfied Legislative
Mandate 20
Other Observations: Planned Entry Exit Capabilities Are Aligned
with Legislation, but Future Expenditure Plans Need to Be
Improved 26
Conclusions 31
Recommendations for Executive Action 32
Agency Comments and Our Evaluation 33
Appendix I Objectives, Scope, and Methodology 36
Appendix II Comments from the Department of Homeland
Security 39
GAO Comments 43
Appendix III Summary of Entry Exit Related Systems 45
Visa Waiver Permanent Program Act Support System 45
National Security Entry Exit Registration System 46
Appendix IV Summary of Legislation Regarding Entry
Exit System Capabilities 48
Appendix V GAO Contacts and Staff Acknowledgments 51
GAO Contact 51
Staff Acknowledgments 51
Tables
Table 1: Primary Inspections by U.S. Ports of Entry (Fiscal Year
2002) 5
Table 2: Foreign Nationals Admitted through Primary and
Secondary Inspections (Fiscal Year 2002) 6
Contents

Page ii GAO-03-563 Entry Exit System Expenditure Planning
Table 3: Summary of INS’s Fiscal Year 2002 Entry Exit System
Expenditure Plan 18
Table 4. Planned Operational Requirements for Entry Exit System 27
Table 5: Key System Capabilities Specified by Legislation
Compared with INS’s Planned Operational Requirements 28
Table 6: Verbatim Text of INS Entry Exit System Expenditure Plan
as Submitted to the Congress 30
Figures
Figure 1: Simplified Diagram of the Border Security Process 6
Figure 2: Simplified Diagram of the Visa Issuance Process 8
Figure 3: Simplified Diagram of the Entry Control Process 11
Figure 4: Simplified Diagram of the Stay Management Process 12
Figure 5: Simplified Diagram of the Exit Control Process 13
Figure 6: Partial DHS Organization Chart Identifying the Border
and Transportation Security Directorate 16

Page iii GAO-03-563 Entry Exit System Expenditure Planning
Abbreviations
ADIS Arrival Departure Information System
APIS Advance Passenger Information System
CCD Consular Consolidated Database
CLASS Consular Lookout and Support System
DHS Department of Homeland Security
DMIA Data Management Improvement Act
FAR Federal Acquisition Regulation
IBIS Interagency Border Inspection System
IIRIRA Illegal Immigration Reform and Immigrant Responsibility
Act of 1996
INS Immigration and Naturalization Service
IT information technology
ITIM Information Technology Investment Management
NCIC National Crime Information Center
NIIS Non-Immigrant Information System
NIST National Institute of Standards and Technology
NSEERS National Security Entry Exit Registration System
OMB Office of Management and Budget
SA-CMM Software Acquisition Capability Maturity Model
SEI Software Engineering Institute
TSA Transportation Security Administration
USA PATRIOT Uniting and Strengthening America by
Providing Appropriate Tools Required to Intercept and
Obstruct Terrorism
US VISIT U.S. Visitor and Immigrant Status Indication Technology
System
VWPPA Visa Waiver Permanent Program Act
This is a work of the U.S. Government and is not subject to copyright protection in the
United States. It may be reproduced and distributed in its entirety without further
permission from GAO. It may contain copyrighted graphics, images or other materials.
Permission from the copyright holder may be necessary should you wish to reproduce
copyrighted materials separately from GAO’s product.

Page 1 GAO-03-563 Entry Exit System Expenditure Planning
June 9, 2003
The Honorable Thad Cochran
Chairman
The Honorable Robert C. Byrd
Ranking Minority Member
Subcommittee on Homeland Security
Committee on Appropriations
United States Senate
The Honorable Harold Rogers
Chairman
The Honorable Martin Olav Sabo
Ranking Minority Member
Subcommittee on Homeland Security
Committee on Appropriations
House of Representatives
The Congress has long recognized the need for a border security system
that collects information about foreign nationals entering and exiting the
United States and identifies those who have overstayed their visits. Seven
years ago, the Congress passed legislation that directed the Immigration
and Naturalization Service (INS)
1
to develop such an entry exit system.
2
More recently, the Congress has passed additional entry exit legislation,
3
requiring, for example, that the system be integrated with other law
1
INS is no longer a distinct federal agency. Effective March 1, 2003, INS became part of at
least three Department of Homeland Security component organizations. However, for
purposes of this report, we continue to refer to INS, as appropriate, because INS is the
focus of the legislative language that this report addresses.
2
Section 110 of the Illegal Immigration Reform and Immigrant Responsibility Act of 1996,
Public Law 104-208 (Sept. 30, 1996).
3
Immigration and Naturalization Service Data Management Improvement Act of 2000,
Public Law 106-215 (June 15, 2000); Visa Waiver Permanent Program Act, Public Law 106-
396 (Oct. 30, 2000); Uniting and Strengthening America by Providing Appropriate Tools
Required to Intercept and Obstruct Terrorism (USA PATRIOT Act) Act of 2001, Public Law
107-56 (Oct. 26, 2001); and Enhanced Border Security and Visa Entry Reform Act of 2002,
Public Law 107-173 (May 14, 2002).
United States General Accounting Office
Washington, DC 20548

Page 2 GAO-03-563 Entry Exit System Expenditure Planning
enforcement databases and that it use biometric technologies
4
to better
identify persons entering and exiting the United States.
To exercise close oversight over the entry exit system,
5
the Congress also
prohibited the INS from obligating funds for the system that were made
available in fiscal year 2002 supplemental appropriations until the agency
submitted to the Senate and House Committees on Appropriations an
expenditure plan (1) that meets the capital planning and investment
control review requirements established by the Office of Management and
Budget (OMB), including Circular A-11, part 3; (2) that complies with the
acquisition rules, requirements, and guidelines and systems acquisition
management practices of the federal government; and (3) that is reviewed
by GAO.
6
This report responds to our legislative mandate to review INS’s fiscal year
2002 entry exit system expenditure plan. On November 15, 2002, INS
provided this plan to the Appropriations Committees, and on December
19, 2002, we received a copy of the plan. As agreed with your offices, our
review objectives were to (1) determine whether the plan satisfied the
legislative conditions and (2) provide observations about the expenditure
plan and INS’s management of the entry exit system. As agreed with your
offices, our review focused not only on the plan, but also on related
system documentation and plans. Our objectives, scope, and methodology
are presented in detail in appendix I.
INS’s fiscal year 2002 expenditure plan, supplemented by related entry exit
system acquisition documentation and plans, partially satisfied relevant
legislative conditions governing INS’s obligation of fiscal year 2002
funding. In particular, INS has either implemented or plans to implement
most of OMB’s capital planning and investment control review
requirements, including those established by Circular A-11, part 3, but has
4
Biometric technologies measure and analyze human physiological and behavioral
characteristics for the purposes of personal identification. Biometric technologies include
fingerprint recognition; hand geometry; and facial, retina, and iris recognition.
5
On April 29, 2003, the Secretary of the Department of Homeland Security renamed the
entry exit system the U.S. Visitor and Immigrant Status Indication Technology System
(US VISIT). Because this name change does not affect the content of this report, we have
not modified the text to change entry exit system to US VISIT.
6
2002 Supplemental Appropriations Act for Further Recovery From and Response to
Terrorist Attacks on the United States, Public Law 107-206 (Aug. 2, 2002).
Results in Brief

Page 3 GAO-03-563 Entry Exit System Expenditure Planning
not yet satisfied two OMB requirements—having a system security plan
and assessing the system’s impact on the privacy of individuals—both of
which are critical to understanding system requirements and ensuring that
acquired system capabilities satisfy these requirements. INS’s plans and
actions to date also are generally consistent with important federal
acquisition rules, requirements, and guidelines and system acquisition
management practices, as defined in such documents as INS’s life cycle
management and investment management guidance and the Federal
Acquisition Regulation. However, before submitting an expenditure plan
to the Appropriations Committees, INS obligated for the system
approximately $9.8 million in fiscal year 2002 supplemental
appropriations. Since then, INS officials told us that they have de-obligated
over $6.6 million that they had obligated after August 2, 2002,
7
and
reclassified those obligations to other available sources.
In addition, we observed that INS’s preliminary plans for the entry exit
system show that it intends for the system to have functional and
performance capabilities that the Congress specified in law. These
capabilities include being able to collect and match alien arrival and
departure data electronically, being accessible to the border management
community, and being able to read tamper-resistant documents with
biometric identifiers. However, we also observed that this first
expenditure plan does not adequately disclose material information about
the system, such as what system capabilities and benefits are to be
delivered, by when, and at what cost. Without sufficiently detailed
information on system plans and progress, the Congress will be impeded
in its oversight efforts for the system.
To improve the content and utility of future entry exit system expenditure
plans, we are making recommendations to the Secretary of Homeland
Security (1) to plan for and implement important system investment and
acquisition management controls and (2) to ensure that the plans provide
sufficient detail about what system capabilities and benefits can be
delivered, what these capabilities will cost, when they will be delivered,
and how the acquisition will be managed to meet these commitments.
7
On August 2, 2002, the Congress passed the supplemental appropriations law (P.L. 107-
206), which prohibited INS from obligating funds for the entry exit system until the agency
submitted an expenditure plan to the Appropriations Committees that satisfied the
conditions under the law mentioned previously.

Page 4 GAO-03-563 Entry Exit System Expenditure Planning
In written comments on a draft of our report signed by the department’s
Assistant Secretary, Bureau of Immigration and Customs Enforcement
(reprinted in app. II, along with our responses), the department did not
explicitly agree or disagree with our conclusions and recommendations.
However, it described several actions that it plans to take that are
consistent with our recommendations.
The department also provided other principal comments. Specifically, it
stated that (1) we failed to consider that the expenditure plan’s lack of
specific detail is attributable to a number of pending policy decisions and
that until these decisions are made it is impossible to provide a detailed
plan; (2) the entry exit system security plan and privacy impact
assessment are addressed in a draft document entitled Technical
Architecture and Security Requirements; (3) we concluded that the entry
exit program office is in compliance with INS’s Information Technology
Investment Management (ITIM) process, and therefore the entry exit
system is in compliance with OMB requirements; and (4) we failed to
consider and incorporate information regarding INS’s obligation of
supplemental appropriations.
We support the department’s planned actions. However, we do not agree
with the four other comments. First, as we state in our report, effective
congressional oversight and informed decision-making require that the
plan disclose a sufficient level and scope of information for the Congress
to understand what system capabilities and benefits are to be delivered, by
when, and at what cost. They also require that the plan address how these
system capability, benefit, schedule, and cost commitments will be met. If
this information was not known because of pending policy issues, this
uncertainty should have been in the plan, along with a timetable for
addressing it. Further, notwithstanding these undecided policy matters,
the plan could still have provided more detailed information, such as
addressing how the acquisition was to be managed. Second, the draft
document that the department provided to us with its comments does not
include either a security plan or a privacy impact assessment. Third, our
report does not conclude that the entry exit program office is in full
compliance with ITIM, and that therefore the entry exit system is in
compliance with OMB requirements. Rather, it concludes that it is
important for INS to focus on implementing the investment management
controls provided for its plan and related documentation. Accordingly, we
recommend in our report that the department fully implement planned
investment management controls in accordance with relevant federal
requirements and guidance. Fourth, we did not include information in our
draft report regarding the department’s obligation of the supplemental
Page 5 GAO-03-563 Entry Exit System Expenditure Planning
appropriations because this information was contained in a letter to us
dated April 7, 2003, which was 4 days after we provided the department
with our draft report. We have since modified this report, as appropriate,
to incorporate the information in the April 7, 2003, letter.
The department also provided additional technical comments, which we
have incorporated as appropriate in our report.
Securing our nation’s borders is a formidable task. The United States
shares over 7,500 miles of land border with Canada and Mexico, and it has
approximately 95,000 miles of shoreline and navigable waterways to
protect. All people and goods that legally enter the United States must
come through one of about 300 land, air, or sea ports of entry and must
undergo what is referred to as “primary inspection.” In fiscal year 2002,
INS reported that over 440 million persons passed through primary
inspections; approximately 81 percent of these inspections were at land
ports of entry (see table 1).
Table 1: Primary Inspections by U.S. Ports of Entry (Fiscal Year 2002)
Inspections
a
Type of port Number Percent
Number of foreign
national inspections
Sea
12,369,035 3 4,994,879
Air
69,679,190 16 36,678,082
Land
358,373,569 81 237,693,265
Total
440,421,794 100 279,366,226
Source: INS.
Note: GAO analysis of INS data.
a
Includes U.S. citizens.
Following primary inspection, some persons seeking admission into the
United States go through a more detailed, secondary inspection before
they can be admitted. In fiscal year 2002, INS reported that about 8 million
of the approximately 279 million foreign nationals entering the United
States were admitted through secondary inspections (see table 2). INS
reported that 738,396 were denied admission.
Background

Page 6 GAO-03-563 Entry Exit System Expenditure Planning
Table 2: Foreign Nationals Admitted through Primary and Secondary Inspections
(Fiscal Year 2002)
Foreign nationals admitted
Type of inspection Number Percent
Primary 270,371,310 97
Secondary 8,256,520 3
Total 278,627,830 100
Source: INS.
Note: GAO analysis of INS data.
As we previously reported,
8
our nation’s current border security process
for controlling the entry and exit of individuals generally consists of four
primary functions: (1) issuing visas, (2) controlling entry, (3) managing
stays, and (4) controlling exit. Figure 1 depicts these functions, each of
which is described below.
Figure 1: Simplified Diagram of the Border Security Process
8
U.S. General Accounting Office, Information Technology: Terrorist Watch Lists Should
Be Consolidated to Promote Better Integration and Sharing, GAO-03-322 (Washington,
D.C.: Apr. 15, 2003).
Overview of the Border
Security Process

Page 7 GAO-03-563 Entry Exit System Expenditure Planning
The visa issuance process begins with the Department of State, which
issues immigrant and nonimmigrant visas
9
to foreign nationals at more
than 200 diplomatic consular posts in approximately 180 countries.
Officials at these consular posts review visa applications, sometimes
interviewing applicants, before issuing a visa. As part of their review of
visa applications, the officials run the applicant’s name through one of the
State Department’s watch lists,
10
the Consular Lookout and Support
System (CLASS),
11
and its Consular Consolidated Database (CCD).
12
If an
application is approved, a visa is issued; if an application is rejected, the
rejection is recorded in CLASS, and the person’s name is electronically
forwarded to the Interagency Border Inspection System (IBIS).
13
The State
Department reports that the majority of visa applications are for
nonimmigrant travel. Canadian citizens and citizens of countries
participating in the Visa Waiver Program
14
who travel to the United States
on business or pleasure for a period of 90 days or less
15
are examples of
9
A nonimmigrant visa authorizes a foreign national to apply for admission to the United
States for a specific purpose and time period. Nonimmigrant visas are valid for 3 months to
10 years, depending on the applicant’s citizenship and other factors.
10
Watch lists, sometimes referred to as lookout, target, or tip-off systems, are databases
that are supported by certain analytical capabilities. The databases contain a wide variety
of data; most contain biographical data, such as name and date of birth, and a few contain
biometric data, such as fingerprints.
11
CLASS is a name check system that contains records of people who may be ineligible to
receive a passport or visa. It is populated from a variety of sources, including intelligence,
immigration, and child support enforcement data. CLASS also includes information on
passports and visas reported lost or stolen.
12
The Consular Consolidated Database determines whether the applicant has previously
applied for a visa or currently has a valid U.S. visa. This database stores information about
visa applications, issuances, and refusals. It obtains information about visa cases every 5 to
10 minutes from each consular post and contains about 58 million visa records.
13
IBIS is a multiagency database of lookout information that alerts inspectors of conditions
that may make travelers inadmissible to the United States. It contains data from law
enforcement and other agencies with inspection responsibilities at ports of entry, including
the Drug Enforcement Administration and the Federal Bureau of Investigation.
14
The Visa Waiver Program permits foreign nationals from designated countries to apply for
admission to the United States for a maximum of 90 days as nonimmigrant visitors for
business or pleasure without first obtaining a nonimmigrant visa. Participating countries
are Andorra, Australia, Austria, Belgium, Brunei, Denmark, Finland, France, Germany,
Iceland, Ireland, Italy, Japan, Liechtenstein, Luxembourg, Monaco, the Netherlands, New
Zealand, Norway, Portugal, San Marino, Singapore, Slovenia, Spain, Sweden, Switzerland,
and the United Kingdom.
15
Other classes of nonimmigrant aliens who are exempt from visa processing requirements
can be found in 8 CFR 212.1.
Issuing Visas

Page 8 GAO-03-563 Entry Exit System Expenditure Planning
two classes of noncitizens that are exempt from these processing
requirements. Figure 2 depicts the visa issuance process.
Figure 2: Simplified Diagram of the Visa Issuance Process
Foreign nationals seeking entry into the United States are screened for
admission by INS or U.S. Customs Service inspectors at official air, land,
or sea ports of entry. Generally, this screening consists of questioning each
traveler regarding his or her identity and purpose of visit. The inspector is
to review the person’s travel documents and query IBIS to determine
whether there is a “lookout” for the person or vehicle. Once the inspector
has the necessary information, an admission decision is made. If additional
review is necessary, the person is referred to secondary inspection, where
a more detailed review of the travel documents, further questioning, and
queries of multiple systems are to occur.
16
Travelers who are deemed
inadmissible are detained, and they are subject to enforcement actions as
required.
16
Additional queries may include the following systems: the Non-Immigrant Information
System; the Central Index System; the Computer Linked Application Information
Management System; the National Automated Immigration Lookout System; the National
Crime Information Center; the Treasury Enforcement Communications System; and the
Automated Biometric Identification System, among others.
Controlling Entr
y

Page 9 GAO-03-563 Entry Exit System Expenditure Planning
Arriving foreign nationals must also complete a paper Form I-94, which is
an arrival/departure record.
17
For each arrival, the inspector is to review
the form for accuracy, and if the foreign national is deemed admissible, the
inspector annotates the admission classification
18
and stamps the “Admit
Until” date on the form. The foreign national is then given the departure
portion of the form for proof of status while in the United States. INS
keeps the arrival portion for entry into the Non-Immigrant Information
System (NIIS) database.
19
The previously described inspection process may vary, depending on
travelers’ nationalities. As of October 2002, the National Security Entry
Exit Registration System (NSEERS) program required nonimmigrant
foreign nationals over the age of 16 from certain countries to register with
INS.
20
At the port of entry, these persons are to be fingerprinted,
photographed, and interviewed under oath at the time they apply for entry
into the United States. The inspector also annotates the Form I-94 with a
Fingerprint Identification Number to show that the person has registered.
(App. III provides more information on NSEERS, as well as the Visa
Waiver Support System, which according to INS officials, are recently
implemented systems that will be integrated into the entry exit system.)
The entry control process also varies by type of port of entry. At air and
sea ports of entry, commercial carriers are required to submit passenger
and crew manifests before arrival. Manifest data are submitted to the
17
The Form I-94 is divided into two parts. The first is an arrival portion, which includes, for
example, the nonimmigrant’s name, date of birth, passport number, airline and flight
number (if applicable), country of citizenship, and address while in the United States. The
second is a departure portion, which includes the name, date of birth, and country of
citizenship. Each form contains a unique number printed on both portions of the form for
the purposes of recording and matching the arrival and departure records of
nonimmigrants.
18
Classifications include passengers under the Visa Waiver Program, passengers in transit,
and passengers on a nonimmigrant visa.
19
The Non-Immigrant Information System collects arrival and departure Form I-94 data and
reports information on confirmed overstays.
20
Temporary foreign visitors (nonimmigrant aliens) who come from certain countries or
who meet a combination of intelligence-based criteria are fingerprinted and photographed
when they enter the United States and are required to report periodically to INS if their stay
exceeds 30 days. Countries currently included under the NSEERS program are Afghanistan,
Algeria, Bahrain, Bangladesh, Egypt, Eritrea, Indonesia, Iran, Iraq, Jordan, Kuwait,
Lebanon, Libya, Morocco, North Korea, Oman, Pakistan, Qatar, Saudi Arabia, Somalia,
Sudan, Syria, Tunisia, United Arab Emirates, and Yemen.

Page 10 GAO-03-563 Entry Exit System Expenditure Planning
Advance Passenger Information System (APIS)
21
and include (among other
things) the person’s full name, date of birth, nationality, and passport
number. Using the manifest data, INS inspectors conduct a name check
through IBIS before the persons arrive, identifying those who will be
subject to secondary inspection.
Land ports of entry differ from air and sea ports of entry in that no
requirements for passenger or crew manifests are imposed on commercial
carriers. Further, the procedures differ for pedestrians and occupants of
vehicles. As a general rule, pedestrians have all travel documents checked,
and if IBIS is available, a name search is conducted. (Exceptions to this
rule are Canadians, who are not required to have a passport when entering
a land port, and Mexicans with a border-crossing card,
22
who are not
required to present a Mexican passport or a U.S. visa.) For vehicles,
license plates are checked through IBIS, and documents and names of the
vehicle’s occupants are checked randomly or when an inspector has
reason to be suspicious. Figure 3 depicts the entry control process.
21
APIS is designed to electronically collect arrival and departure manifests from
commercial carriers.
22
A border-crossing card permits the holder to enter for business or pleasure, stay in the
United States for 72 hours or less, and go no farther than 25 miles from the border.

Page 11 GAO-03-563 Entry Exit System Expenditure Planning
Figure 3: Simplified Diagram of the Entry Control Process
Until recently, foreign nationals admitted into the United States were not
actively monitored. However, with the implementation of NSEERS, certain
foreign national males over the age of 16 are now required, within 30 days
of arrival, to report to an INS office and register, a process that includes
providing information consistent with their visas, such as proof of
residence and proof of employment. If the foreign national stays in the
United States for more than 1 year, he must also report to a designated INS
location within 10 days of each registration anniversary. If the foreign
national changes his address, school, or employer, he is required to notify
INS by mail within 10 days. Those who violate these rules will have their
photographs, fingerprints, and other information added to the National
Managing Stays

Page 12 GAO-03-563 Entry Exit System Expenditure Planning
Crime Information Center (NCIC) “wants and warrants” list for
enforcement purposes.
23
NSEERS violators who are caught by police are
transferred to INS custody for removal or criminal prosecution. Figure 4
depicts the stay management process.
Figure 4: Simplified Diagram of the Stay Management Process
At air and sea ports of entry, carriers are responsible for collecting from
exiting foreign nationals the departure portions of the Form I-94 and for
forwarding them to INS, which in turn sends them to a data entry
contractor for manual input into the Non-Immigrant Information System.
Carriers are also required to electronically submit to APIS manifest
information of passengers leaving the United States from an air or sea port
of entry. The departure manifest information is transmitted from APIS to
the Arrival Departure Information System (ADIS), which uses name-
matching algorithms to match the arrival and departure records and
identify persons who have overstayed their authorized visits. At land ports
of entry, there is no collection point for the departure portion of the Form
I-94. The foreign national is responsible for returning the departure
portion, although there is no penalty for not doing so, unless the person is
subject to NSEERS requirements. Persons subject to NSEERS must depart
the United States from an INS-designated port of entry and report to an
INS agent for examination and endorsement of departure. If these persons
23
The National Crime Information Center provides information on wanted persons and
criminal histories. Law enforcement officers throughout the United States check this
database regularly in the course of traffic stops and routine encounters.
Controlling Exit

Page 13 GAO-03-563 Entry Exit System Expenditure Planning
do not report their exit, they become ineligible to return to the United
States. The exit control process is depicted in figure 5.
Figure 5: Simplified Diagram of the Exit Control Process
Legislation defines the capabilities that the entry exit system is to have.
The “pre-9/11” laws defining these capabilities are the Illegal Immigration
Reform and Immigrant Responsibility Act of 1996 (IIRIRA),
24
the
Immigration and Naturalization Service Data Management Improvement
Act of 2000,
25
and the Visa Waiver Permanent Program Act.
26
The “post-
9/11” laws are the USA PATRIOT Act,
27
the Aviation and Transportation
Security Act,
28
and the Enhanced Border Security and Visa Entry Reform
Act of 2002.
29
Among other things, Section 110 of IIRIRA directed the Attorney General
to develop an automated entry exit control system to collect records of
departure from every alien leaving the United States and match it with the
24
Public Law 104-208 (Sept. 30, 1996).
25
Public Law 106-215 (June 15, 2000).
26
Public Law 106-396 (Oct. 30, 2000).
27
Public Law 107-56 (Oct. 26, 2001).
28
Public Law 107-71 (Nov. 19, 2001).
29
Public Law 107-173 (May 14, 2002).
Congress Has Specified
Entry Exit System
Capabilities in Legislation

Page 14 GAO-03-563 Entry Exit System Expenditure Planning
alien’s record of arrival. It also required that the system provide on-line
searching procedures to identify each lawfully admitted nonimmigrant
who remains in the United States beyond his or her authorized period.
The Immigration and Naturalization Service Data Management
Improvement Act amended Section 110 of IIRIRA by replacing it in its
entirety. This act, among other things, requires that the entry exit system
integrate arrival and departure information on aliens required under
IIRIRA and contained in Department of Justice (including INS) and State
Department databases. Further, the act specifies that the system be
implemented at all airports and seaports by December 31, 2003; the 50
busiest land ports by December 31, 2004; and all remaining ports no later
than December 31, 2005.
The Visa Waiver Permanent Program Act, among other things, requires the
Attorney General, no later than October 1, 2001, to develop and implement
at airports and seaports a fully automated system to control entry and exit
of aliens who enter the United States under the Visa Waiver Program. The
act also requires that, by October 1, 2002, inspectors at the ports of entry
have access to any State Department or INS photograph and information
on whether the alien has been determined to be ineligible to be admitted
to the United States or receive a visa. Further, the act requires that visa
waiver applicants be checked against lookout (i.e., watch list) systems,
and that by October 1, 2007, aliens applying for a visa waiver have a
machine-readable passport.
Since September 11, 2001, three additional laws address, among other
things, an alien entry exit control system. The USA PATRIOT Act
mandates that this system be capable of interfacing with other law
enforcement agencies, and that it use biometric technology and tamper-
resistant documents. The Aviation and Transportation Security Act
requires air carriers to electronically transmit manifest information for all
international flight passengers and crew members before landing at a U.S.
airport. The Enhanced Border Security and Visa Entry Reform Act further
requires the use of biometrics in travel documents by October 26, 2004; it
expands the passenger arrival manifest requirement in the Aviation and
Transportation Security Act to sea carriers and to air and sea departures;
and it requires compliance for both no later than January 1, 2003.
Appendix IV provides more information on the legislatively mandated
capabilities for an entry exit system.
Page 15 GAO-03-563 Entry Exit System Expenditure Planning
In July 2002, the administration issued a national strategy for homeland
security.
30
This strategy, among other things, aligns and focuses homeland
security functions into six mission areas, one of which is border and
transportation security.
31
To better address the issues of border and
transportation security, the strategy identifies several initiatives, including
• creating “smart borders” to provide greater security, including the
development and deployment of the statutorily mandated entry exit
system; and
• ensuring accountability in border and transportation security by
consolidating the current border and transportation security agencies
under a new department of homeland security.
In November 2002, the Congress passed and the President signed the
Homeland Security Act of 2002,
32
which established this new Department
of Homeland Security (DHS) to provide greater accountability over critical
homeland security missions and unity of purpose among the agencies
responsible for them.
The administration’s national strategy also proposed having a single entity
to manage who and what enters the United States. Under the new
department, this single entity is the Border and Transportation Security
Directorate. Before this, responsibility and accountability for border
security were vested primarily with INS, which was part of the Justice
Department; the Customs Service, which was part of the Department of
the Treasury; the Transportation Security Administration (TSA), which
was part of the Department of Transportation; and the Bureau of Consular
Affairs, which is part of the State Department. Effective March 1, 2003,
DHS merged within its Border and Transportation Security Directorate
three of these four agencies—INS, Customs, and TSA. The goal in doing so
is to better manage and coordinate port of entry activities, lead efforts to
create a border of the future, and secure our nation’s transportation
systems. Also, the Secretary of Homeland Security has the authority to
30
Office of Homeland Security, National Strategy for Homeland Security (Washington,
D.C.: July 2002).
31
The other critical mission areas are intelligence and warning, domestic counterterrorism,
protecting critical infrastructure, defending against catastrophic terrorism, and emergency
preparedness and response.
32
Homeland Security Act of 2002, Public Law 107-296 (Nov. 25, 2002).
Overview of the
President’s Homeland
Security Strategy and
Department of Homeland
Security

Page 16 GAO-03-563 Entry Exit System Expenditure Planning
issue regulations regarding the issuance of visas. The regulations will be
implemented through the State Department. (See fig. 6 for a partial
organization chart of the Border and Transportation Security Directorate.)
Figure 6: Partial DHS Organization Chart Identifying the Border and Transportation
Security Directorate
The entry exit program was established to integrate the people, processes,
and technologies needed to satisfy the legislative mandates. The program
includes each of the four border security process functions: issuing visas,
controlling entry, managing stays, and controlling exit. Additionally, the
program is intended to cover the people responsible for implementing the
process, the technology to support the process, and the physical
infrastructure (e.g., vehicle and pedestrian traffic lanes and facilities)
needed to support the process.
For fiscal year 2002, the conference report for the first supplemental
appropriations act
33
recommended that INS use $13.3 million in
appropriations for the development of an automated entry exit system.
The Congress prohibited INS from obligating these funds for the system
33
H.R. Conf. Rep. No. 107-350, at 416 (2001).
Brief Description of the
Entry Exit Program

Page 17 GAO-03-563 Entry Exit System Expenditure Planning
until the agency submitted to the Appropriations Committees an
expenditure plan (1) that meets the capital planning and investment
control review requirements established by OMB, including Circular A-11,
part 3; (2) that complies with the acquisition rules, requirements, and
guidelines and systems acquisition management practices of the federal
government; and (3) that is reviewed by GAO.
On November 15, 2002, INS submitted to its Senate and House
Appropriations Subcommittees a one-page plan for spending the $13.3
million for the entry exit system. In summary, the plan allocated the $13.3
million to 10 areas, the largest area being contract support for program
management activities ($5.6 million). Other major areas included the
design, development, and deployment of the Visa Waiver Permanent
Program Act Support System ($2.1 million); the assessment of facilities at
every port of entry along the Mexican and Canadian borders ($1.4 million);
and the development of standards for biometrics identifiers
34
($2.1
million). Table 3 summarizes INS’s entry exit system expenditure plan.
34
The National Institute of Standards and Technology (NIST) is to test biometrics and assist
in developing standards for biometric identifiers, as required by legislation. The Office of
Science and Technology Policy is to assist and advise INS on possible biometric identifiers.

Page 18 GAO-03-563 Entry Exit System Expenditure Planning
Table 3: Summary of INS’s Fiscal Year 2002 Entry Exit System Expenditure Plan
Area of expenditure Amount
1. Entry exit support contract activities (e.g., evaluating the proposals; developing the
concept of operations, business case, and request for proposal)
$5,554,000
2. Design, development, and deployment of the Visa Waiver Support System 2,050,000
3. Assessment of the current facilities at every land border port along the Canadian and
Mexican borders
1,425,000
4. Development of biometrics standards and testing of possible biometric identifiers 2,060,000
5. Prototyping of proposed systems at various ports of entry 863,000
6. IBIS support activities 560,000
7. Joint TSA/Customs/State/INS/Department of Agriculture project with United Airlines to
develop an expedited process to inspect returning U.S. citizens
400,000
8. Travel 210,800
9. Entry exit program office operations 159,000
10. Livescan fingerprint units 18,200
Total $13,300,000
Source: INS.
Note: GAO analysis of INS data.
In fiscal year 2003, Justice requested $380 million for the entry exit
program—$362 million in new funding and $18 million provided in fiscal
year 2003 base resources.
35
According to INS officials, $334 million of this
amount will be used for facility improvements. In conjunction with the
Consolidated Appropriations Resolution, 2003,
36
the conference report
37
recommended $362 million for the entry exit program in fiscal year 2003
funds.
In March 2002, INS chartered an Entry Exit Program Team consisting of
representatives from INS, Customs, TSA, and the Bureau of Consular
Affairs, with INS serving as the program lead; the team reports to an
35
According to Justice and OMB officials, the $18 million requested in base resources
reflects prior year funding to INS for several smaller initiatives related to the entry exit
system.
36
Public Law 108-7 (Feb. 20, 2003).
37
H.R. Conf. Rep. No. 108-10, at 623 (2003).

Page 19 GAO-03-563 Entry Exit System Expenditure Planning
interagency board comprising senior leadership from these four agencies.
38
The team is responsible for
• managing program resources (i.e., budgetary planning, formulation,
execution, and control);
• reporting to the Congress and other key stakeholders, as necessary; and
• managing the acquisition, including defining and establishing program
management controls, developing program plans and baselines, and
managing all aspects of the entry exit system life cycle.
As currently envisioned, the program will be placed organizationally
within DHS’s Bureau of Immigration and Customs Enforcement, which is
part of the department’s Border and Transportation Security Directorate
(see fig. 6), previously mentioned. With the transition to the new
department, the program manager also stated that the program’s
governance and management structure is undergoing change.
As previously noted, the entry exit system is one of three parts of the
whole entry exit program—the technologies—the other two parts being
people and processes. As planned, the system is to provide automated
support in identifying and preventing unlawful persons from entering the
United States, as well as managing the stay and exit of those lawfully
admitted. To do this, plans indicate that the system is to share vital border
control information so as to alert border officials of national security
threats. It is also to help coordinate the enforcement of immigration laws
for alien overstays.
DHS’s Bureau of Immigration and Customs Enforcement plans to acquire
the entry exit system through a two-phase competitive acquisition process.
The first phase is referred to as a pilot demonstration. In this phase, two or
more contractors are to be awarded contracts to develop and pilot test
system solutions. Following an evaluation of each pilot system, a contract
is to be awarded to the winning contractor for full-scale development and
implementation of the entry exit system. According to the entry exit
program manager, INS has developed costs and milestones for the system
38
According to the entry exit program manager, the Homeland Security Council’s Principals
and Deputies Committees make up the external governing body for the entry exit program.
The Principals Committee is made up of the major department secretaries, while the
deputy secretaries of the departments make up the Deputies Committee.
Page 20 GAO-03-563 Entry Exit System Expenditure Planning
acquisition. However, INS did not respond to our requests for this
information, citing the sensitive nature of the information as its reason.
The Congress limited INS’s ability to obligate fiscal year 2002 appropriated
funds for the entry exit system until INS submitted to the Appropriations
Committees an expenditure plan (1) that meets the capital planning and
investment control review requirements established by OMB, including
Circular A-11, part 3; (2) that complies with the acquisition rules,
requirements, and guidelines and systems acquisition management
practices of the federal government; and (3) that is reviewed by us.
INS submitted an expenditure plan to its Senate and House Appropriations
Subcommittees on November 15, 2002. This plan and related
documentation partially satisfied the first condition and generally satisfied
the second condition, and we have satisfied the third with this report.
According to the entry exit program manager, INS’s efforts to satisfy the
two conditions are a by-product of its policies and practices for acquiring
information technology (IT) systems, which it is following, and which are
aligned with federal capital planning and acquisition requirements and
guidance.
However, INS has obligated at least part of the $13.3 million recommended
for the entry exit system before submitting the plan. Since then, INS
officials told us that they have de-obligated over $6.6 million that they had
obligated after August 2, 2002,
39
and reclassified those obligations to other
available sources of base “Enforcement and Border Affairs” fiscal year
2002 funding.
39
On August 2, 2002, the Congress passed the supplemental appropriations law (P.L. 107-
206), which prohibited INS from obligating funds for the entry exit system until the agency
submitted an expenditure plan to the Appropriations Committees that satisfied the
conditions under the law mentioned previously.
Fiscal Year 2002
Expenditure Plan
Partially Satisfied
Legislative Mandate

Page 21 GAO-03-563 Entry Exit System Expenditure Planning
OMB’s IT capital planning and investment control review policies are
intended to help agencies achieve performance goals and objectives with
minimal risk, lowest life cycle costs, and greatest benefits to the agency’s
business.
40
OMB requires, among other things, that agencies establish a
process that defines how the agency (1) selects projects included in its IT
portfolio; (2) controls these projects to achieve the intended cost,
schedule, and performance outcomes; and (3) evaluates IT projects’
performance to maintain a positive return on investment. OMB also
requires that agencies (1) develop a system acquisition strategy;
(2) conduct an alternatives analysis that, among other things, addresses
replaced systems savings and a savings recovery schedule; (3) comply
with agencies’ enterprise architectures
41
in developing and acquiring IT
systems; and (4) use a performance-based management system to monitor
progress against established project performance goals. Additionally, OMB
requires that IT projects (1) ensure that a system security plan is
developed and implemented, so that appropriate controls are defined,
established, and continually assessed for effectiveness, and (2) perform a
system privacy impact assessment, so that relevant privacy issues and
needs are understood and appropriately addressed early and continuously
in the system life cycle.
While the expenditure plan does not explicitly address OMB’s
requirements, related INS documents and plans satisfy most, but not all, of
the requirements. For example, INS has established a capital planning and
investment control process that defines how INS selects, controls, and
evaluates its IT projects. This process describes (1) controls used to create
the IT portfolio; (2) procedures for measuring projects against their costs,
schedule, and benefits; and (3) measures used to determine the IT
40
OMB Circular A-130, Management of Federal Information Resources (Washington, D.C.:
Nov. 28, 2000); OMB Circular A-11, part 3, Planning, Budgeting, and Acquisition of
Capital Assets (Washington, D.C.: July 2000).
41
An enterprise architecture is an essential tool for effectively and efficiently engineering
business processes and for implementing and evolving their supporting systems. It consists
of systematically derived and captured descriptions—in useful models, diagrams, and
narrative—of the mode of operation for a given enterprise. The architecture describes the
enterprise’s operations in both (1) logical terms, such as interrelated business processes
and business rules, information needs and flows, and work locations and users; and
(2) technical terms, such as hardware, software, data, communications, and security
attributes and performance standards. It provides these perspectives both for the
enterprise’s current or “as is” environment and for its target or “to be” environment, as well
as a transition plan for moving from the “as is” to the “to be” environment. See U.S. General
Accounting Office, Information Technology: Enterprise Architecture Use Across the
Federal Government Can Be Improved, GAO-02-6 (Washington, D.C.: Feb. 19, 2002).
INS Satisfied Most, but Not
All, of OMB’s Capital
Planning and Investment
Control Review
Requirements

Page 22 GAO-03-563 Entry Exit System Expenditure Planning
projects’ actual return on investment. The process also identifies several
decision points for review and approval. For example, approval by INS’s
Investment Approval Board
42
of the business case (cost/benefit analysis,
risk analysis, and alternatives analysis) is required before the project team
defines system requirements. INS has not yet developed a business case
for the entry exit program.
Further, INS has developed an entry exit system acquisition strategy.
Under this strategy, INS intends to acquire the system in two phases. In
the first phase, it plans to award contracts to multiple vendors to develop
prototype versions of the system and to demonstrate their capabilities
against requirements, on a pilot basis, at a simulated port of entry. In the
second phase, INS plans to award a contract to develop, integrate, and
implement an operational entry exit system. Additionally, it has developed
an alternatives analysis, and, according to the entry exit program manager,
INS’s fiscal year 2004 Exhibit 300
43
for the entry exit program addresses
the potential savings associated with replacing existing systems and a
schedule for achieving those savings. In addition, preliminary planning
documents indicate that INS plans to comply with its enterprise
architecture, and that it intends to apply earned value management
standards and techniques to monitor and control costs and to measure
progress against established performance goals.
However, INS has yet to develop a security plan and privacy impact
assessment for the entry exit system, both of which are important to
understanding system requirements and ensuring that the proper
safeguards are in place to protect system data and resources. According to
INS officials, the agency has not developed a security plan and privacy
impact assessment because it is too early in the system development life
cycle to do so. This is not consistent with system acquisition best practices
and federal guidance, which advocate understanding and defining security
and privacy requirements both early and continuously in a system’s life
cycle. Until these important requirements are satisfied, the basis for
42
The board serves as the decision-making authority for all investment decision points,
serves as the review authority for projects, and oversees the implementation of and
adherence to the INS investment process.
43
Exhibit 300 is designed to assist OMB during budget review. It includes information that
demonstrates compliance with capital planning and investment control policies, and it
justifies new or continued funding for major acquisitions by demonstrating, among other
things, acquisition planning, risk mitigation and management planning, and measurable
benefits.

Page 23 GAO-03-563 Entry Exit System Expenditure Planning
further entry exit system definition and acquisition will be limited, thereby
introducing the risk that security and privacy will not be effectively and
efficiently addressed.
Federal acquisition rules, requirements, guidelines, and management
practices provide an acquisition management framework that is based on
the use of rigorous and disciplined processes for planning, managing, and
controlling the acquisition of IT resources.
44
These acquisition
management processes are also embodied in published best practices
models, such as the Software Acquisition Capability Maturity Model
®
developed by Carnegie Mellon University’s Software Engineering Institute
(SEI).
45
SEI’s model explicitly defines acquisition process management
controls that are recognized hallmarks of successful organizations and
that, if implemented effectively, can greatly increase the chances of
acquiring software-intensive systems that provide promised capabilities on
time and within budget. Key processes include the following:
• Acquisition planning. Ensures that reasonable planning for the
acquisition is conducted and that all aspects of the total acquisition effort
are included in these plans.
• Solicitation. Ensures that a request for proposal that delineates a project’s
requirements is prepared and, consistent with relevant solicitation laws
and regulations, that a contractor is selected that can most cost-effectively
satisfy these requirements.
• Requirements development and management. Establishes and maintains
a common and unambiguous definition of software requirements among
the acquisition team, the system users, and the development contractor.
• Project management. Provides for management of the activities within the
project office and supporting contractors to ensure a timely, efficient, and
cost-effective acquisition.
• Contract tracking and oversight. Ensures that the development
contractor performs according to the terms of the contract; needed
44
See, for example, the Clinger-Cohen Act of 1996 (P.L. 104-106), OMB Circular A-130, and
the Federal Acquisition Regulation.
45
Carnegie Mellon Software Engineering Institute, Software Acquisition Capability
Maturity Model (SA-CMM
®
), Version 1.03 (March 2002).
INS Generally Satisfied
Key Federal Acquisition
Rules, Requirements, and
Guidelines and Systems
Acquisition Management
Practices

Page 24 GAO-03-563 Entry Exit System Expenditure Planning
contract changes are identified, negotiated, and incorporated into the
contract; and contractor performance issues are identified early, when
they are easier to address.
• Evaluation. Determines whether the acquired products and services
satisfy contract requirements before acceptance.
Within these key processes, SEI identifies practices that are needed to
effectively execute each process. Among others, these practices include
(1) having a written policy, (2) assigning responsibility for the acquisition,
(3) developing and adhering to a plan, (4) performing management review
activities, and (5) measuring the status of key activities and using these
measurements to make decisions.
INS plans generally satisfy SEI’s acquisition processes and practices. For
example, INS’s governing acquisition policy and supporting procedures for
acquiring and implementing the entry exit system are provided by INS’s
Systems Development Life Cycle,
46
its Information Technology Investment
Management process,
47
and the Federal Acquisition Regulation,
48
which our
analysis shows are generally consistent with SEI’s acquisition model. (See
app. I for a description of our analysis.) Further, responsibility for
acquiring and implementing the entry exit system was assigned to INS
(and now to DHS’s Bureau of Immigration and Customs Enforcement).
INS has developed an acquisition plan that outlines its approach and
strategy for acquiring the entry exit system. Additionally, INS has issued a
request for information to solicit input from development contractors on
the capabilities of their respective commercial products and services to
assist in developing system requirements, and it has developed procedures
and criteria for evaluating contractor proposals and selecting a contractor
to develop the entry exit system. Further, through its Information
Technology Investment Management process, INS plans to measure the
46
The Systems Development Life Cycle specifies development activities to be performed,
the products to be generated, and the decision points to determine whether the project is
ready for the next phase.
47
The Information Technology Investment Management process specifies the process and
activities for management oversight of IT projects, including decision points for measuring
and monitoring progress on IT projects to ensure that they are meeting cost, schedule, and
performance goals.
48
The Federal Acquisition Regulation specifies acquisition activities to be performed and
products to be generated.

Page 25 GAO-03-563 Entry Exit System Expenditure Planning
status and progress of acquisition activities and use this information for
investment decision-making.
According to the entry exit program manager, INS has made a
commitment to following rigorous and disciplined processes and practices
in acquiring the entry exit system because this is what its governing policy
and procedures require. If implemented effectively, such processes and
practices can minimize the acquisition and deployment risks associated
with the entry exit system.
On December 19, 2002, we received a copy of the initial expenditure plan
that INS submitted to the Congress, and on January 17, 2003, INS provided
us with most of the supporting acquisition management documentation we
requested. We reviewed the plan and documentation, and the results of
our review are provided in this report.
In addition to requiring the expenditure plan to satisfy the above three
conditions, the Congress also limited INS’s ability to obligate funds for the
entry exit system until INS submitted the plan to the Appropriations
Committees. However, INS obligated entry exit system funding before
submitting the plan. Specifically, as part of a January 6, 2003, briefing on
planned fiscal year 2003 entry exit spending, INS reported to its House
Appropriations Subcommittee that, as of September 30, 2002, it had
obligated approximately $9.8 million of the $13.3 million recommended for
the entry exit system to perform tasks described in its expenditure plan.
Since then, INS officials told us that they have de-obligated over $6.6
million that they had obligated after August 2, 2002,
49
and reclassified those
obligations to other available sources of base “Enforcement and Border
Affairs” fiscal year 2002 funding.
49
On August 2, 2002, the Congress passed the supplemental appropriations law (P.L. 107-
206), which prohibited INS from obligating funds for the entry exit system until the agency
submitted an expenditure plan to the Appropriations Committees that satisfied the
conditions under the law mentioned previously.
GAO Reviewed
Expenditure Plan
Expenditure Plan
Submitted to the Congress
after Funds Were
Obligated

Page 26 GAO-03-563 Entry Exit System Expenditure Planning
Recent legislation has defined the capabilities that the entry exit system is
to provide, and INS’s preliminary plans show that it intends for the system
to provide these capabilities. However, INS’s first entry exit system
expenditure plan does not adequately disclose material information about
the system. Without sufficiently detailed information on system plans and
progress, the Congress will be impeded in its efforts to oversee the system
and constrained in its ability to provide timely guidance and release of
funding.
As discussed in the Background section of this report, various laws have
defined the types of capabilities that the entry exit system is to provide.
(See app. IV for a more detailed summary of the legislation.) For example,
the system must, among other things, (1) collect and match alien arrival
and departure data electronically; (2) be accessible to the border
management community, including consular officers, federal inspection
agents, and law enforcement and intelligence agencies responsible for the
identification and investigation of foreign nationals; and (3) support
machine-readable, tamper-resistant documents containing biometric
identifiers at U.S. ports of entry.
Initial INS plans for the entry exit system are generally aligned with these
legislatively directed system capabilities. For example, the operational
capabilities for the planned system include, among other things,
(1) electronically recording and matching arrivals and departures for the
purpose of identifying visa overstays; (2) interoperating with other entities
involved in border management, including law enforcement and
intelligence agencies; and (3) implementing a biometric standard on all
travel documents issued on or after October 26, 2004.
50
Table 4 provides a
list of the high-level operational requirements defined in preliminary
system plans, and table 5 provides a detailed comparison to the key
legislative requirements.
50
The biometric standard will be selected by NIST. The USA PATRIOT Act, as amended by
the Enhanced Border Security and Visa Entry Reform Act of 2002, Public Law 107-173 (May
14, 2002), requires NIST to develop and certify a technology standard that can be used to
verify the identity of persons applying for a U.S. visa or using a visa to enter the United
States.
Other Observations:
Planned Entry Exit
Capabilities Are
Aligned with
Legislation, but
Future Expenditure
Plans Need to Be
Improved
Preliminary Plans Provide
for Implementing System
Capabilities Cited in
Legislation

Page 27 GAO-03-563 Entry Exit System Expenditure Planning
Table 4. Planned Operational Requirements for Entry Exit System
Requirement number Description of requirement
1 Record pertinent information before the arrival of persons to the United States, such as visas and
immigration petitions and applications.
2 Record the arrival and departure of aliens; record changes in a visitor’s status; identify those persons
who have remained in the United States beyond their authorized period; and enable the reporting of
overstay statistics to Congress.
3 Facilitate identification of lawfully admitted non-U.S. citizens.
4 Enable the biometric standard selected by the National Institute for Standards and Technology and
consistent with the International Civil Aviation Organization’s standards.
5 Include the biometric standard on all travel documents issued on or after October 26, 2004.
6 Develop a unified workflow that integrates the activities of all agencies supporting border
management.
7 Be interoperable with other entities as appropriate, including law enforcement and intelligence
agencies.
8 Provide access to, exchange, and integrate alien arrival and departure information that is in an
electronic format in the databases of the Departments of Justice and State.
9 Develop a capability to exchange information between existing and future systems among border
management agencies (within the requirement of the law) regardless of what agency owns the
system.
10 Notify appropriate authorities as required.
11 Provide improved decision support to inspectors, adjudicators, consular officers, and other appropriate
personnel, including access to fully integrated lookout information, comprehensive travel document
information (including immediate access to nonimmigrant visa and immigrant visa data), and alien
overstay alerts.
Source: INS.

Page 28 GAO-03-563 Entry Exit System Expenditure Planning
Table 5: Key System Capabilities Specified by Legislation Compared with INS’s Planned Operational Requirements
Legislative requirement for entry exit system
INS operational requirement
in table 4
The term “integrated entry and exit data system” means an electronic system that
• provides access to and integrates alien arrival and departure data that are (1) authorized or
required to be created or collected under law; (2) in an electronic format; and (3) in a Justice or
State Department database, including those created or used at ports of entry and at consular
offices;
• produces a report of arriving and departing aliens by country of nationality, classification as an
immigrant or nonimmigrant, and date of arrival in and departure from the United States;
• matches an alien’s available arrival data with the alien’s available departure data;
• identifies lawfully admitted nonimmigrants who may have remained in the United States beyond
the period authorized by the Attorney General; and
• uses available data to permit the Attorney General to generate reports, including (1) number of
departure records collected by nationality; (2) number of departure records that were
successfully matched to records of arrival, by nationality and classification as an immigrant or
nonimmigrant; (3) number of aliens who arrived pursuant to a nonimmigrant visa or the Visa
Waiver Program, for whom no matching departure data have been obtained as of the end of the
alien’s authorized period of stay, by nationality and arrival date in the United States; and
(4) number of lawfully admitted nonimmigrants identified as visa overstays, by nationality.
2, 3, 8, 11
The entry exit system will be implemented at airports and seaports by December 31, 2003; at the
50 busiest land border ports of entry by December 31, 2004; and at all remaining ports by
December 31, 2005.
2, 11
By October 1, 2001, the Attorney General shall develop and implement a fully automated entry
exit control system to collect a record of arrival and departure for every alien who arrives and
departs by sea or air at a U.S. port of entry and is provided a waiver under the Visa Waiver
Program.
2, 3
By October 1, 2002, the system shall enable immigration officers conducting inspections at ports
of entry to obtain, with respect to aliens seeking a waiver under the Visa Waiver Program, (1) any
photograph of the alien that is contained in the records of the State Department or INS and
(2) information on whether the alien has ever been determined to be ineligible to receive a visa or
be admitted to the United States.
1, 8, 11
On or after October 1, 2007, an alien applying for U.S. entrance under the Visa Waiver Program
must have a valid unexpired passport that meets internationally accepted standards for machine
readability.
3
Countries designated to participate in the Visa Waiver Program before May 1, 2000, shall issue
machine-readable passports no later than October 1, 2003.
3
By October 1, 2002, no visa waiver may be provided to an alien arriving by air or sea at a port of
entry on a carrier unless the carrier is electronically transmitting passenger data to the entry exit
system.
2, 3
All Visa Waiver Program applicants must be checked against lookout systems. 1, 3, 7
Not less than 1 hour before arrival at port of entry, signatory aircraft transporting Visa Waiver
Program aliens must electronically furnish the passenger data required by regulations.
2, 3
The system shall contain sufficient data to permit the Attorney General to calculate, for each Visa
Waiver Program country and each fiscal year, the portion of nationals of that country who arrive
under the program at air and sea ports of entry but for whom no record of departure exists,
expressed as a percentage of the total number of such visa waiver aliens for the particular
country.
2
System shall maintain, for a minimum of 10 years, information about each application for
admission made by an alien seeking a waiver under the Visa Waiver Program.
1, 11
Focus of system development shall be (1) on the use of biometric technology and (2) on tamper-
resistant documents readable at ports of entry.
4, 5

Page 29 GAO-03-563 Entry Exit System Expenditure Planning
Legislative requirement for entry exit system
INS operational requirement
in table 4
System must be accessible to (1) all consular officers responsible for visa issuance, (2) all federal
inspection agents at all U.S. border inspection points, and (3) all law enforcement and intelligence
responsible for investigation or identification of aliens.
1, 6, 7, 9, 10, 11
The entry exit system must be able to interface with law enforcement databases for use by federal
law enforcement to identify and detain individuals who pose a threat to the national security of the
United States.
7, 9, 10
No later than October 26, 2004, the Secretary of State and the Attorney General shall issue to
aliens only machine-readable, tamper-resistant visas and other travel and entry documents that
use biometrics.
4, 5, 8
In addition to the requirement for biometric identifiers, name-search capacity and support must
also be implemented between 18 months and 4.5 years of enactment.
2, 11
Not later than October 26, 2004, the Attorney General and the Secretary of State shall install at all
U.S. ports of entry equipment and software to allow biometric comparison and authentication of all
U.S. visas and other travel and entry documents issued to aliens.
4, 5, 8
Not later than January 1, 2003, arrival and departure manifests must be electronically provided for
each passenger (including crew members and any other occupants) for air and sea carriers at port
of entry. The manifest shall include (1) complete name; (2) date of birth; (3) citizenship; (4) sex;
(5) passport number and country of issuance; (6) country of residence; (7) U.S. visa number, date,
and place of issuance, where applicable; (8) alien registration number, where applicable; (9) U.S.
address while in the United States; and (10) other information the Attorney General and the
Secretaries of State and the Treasury determine necessary for the identification of persons, for the
enforcement of immigration laws, and to protect safety and national security.
2, 3, 6, 11
Upon request, information provided to the Department of Transportation or the U.S. Customs
Service may be shared with other federal agencies for the purpose of protecting national security.
6, 7, 8, 9, 10, 11
Sources: Section 110, Public Law 104-208 (Sept. 30, 1996); Public Law 106-215 (June 15, 2000); Public Law 106-396 (Oct. 30, 2000); Public Law 107-56 (Oct. 26, 2001); Public Law 107-71 (Nov. 19,
2001); and Public Law 107-173 (May 14, 2002).
Note: GAO analysis of cited legislation and INS entry exit system operational requirements.
The legislative requirement to submit an expenditure plan for the entry
exit system to the Appropriations Committees is intended to provide
lawmakers with a sufficient understanding of the system acquisition to
permit effective oversight and to allow for informed decision-making
about the use of appropriated funds. For this to occur, however, our prior
experience in working with the Congress and other agencies in developing
and implementing expenditure plans shows that these plans need to
disclose a sufficient level and scope of information for the Congress to
understand what system capabilities and benefits are to be delivered, by
when, and at what cost, and what progress is being made against the
commitments that were made in prior expenditure plans. Further, our
experience shows that the plans should disclose how the acquisition will
be managed to provide reasonable assurance that system capability,
benefit, schedule, and cost commitments will be met. In effect, the
expenditure plans can be viewed as contractual arrangements with the
committees. Such treatment is consistent with expenditure planning
System Acquisition
Commitments and
Progress Need to Be
Addressed in Future
Expenditure Plans
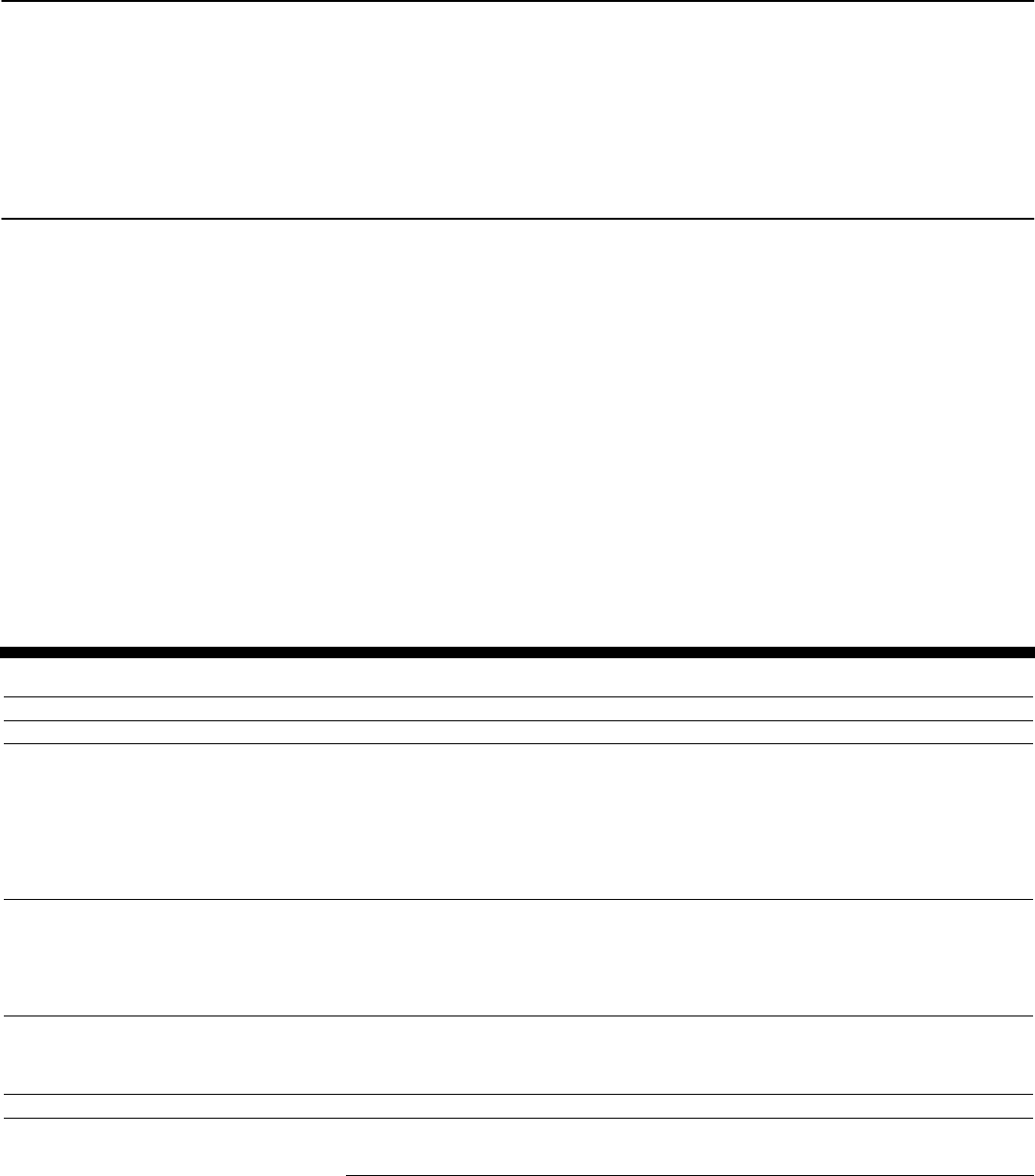
Page 30 GAO-03-563 Entry Exit System Expenditure Planning
precedents set with the Internal Revenue Service and the former U.S.
Customs Service on their respective system modernization programs.
51
INS’s first expenditure plan does not contain the level and scope of
information needed for the Congress to understand its plans and
commitments relative to system capabilities, benefits, schedules, and
costs. More specifically, this first plan only identifies general “areas of
expenditure” and associated funding amounts (see table 6 for the verbatim
text of the plan as submitted). According to INS officials, this is because
the expenditure plan was developed on the basis of Justice Department
guidance, which did not require more detailed information. However, they
said that future plans will include more detailed and complete information
on system capabilities, benefits, schedules, and costs, but they did not
provide supporting documentation or specific details. Without this level of
detail, the Congress will be denied the information needed to allow it to
oversee plans and progress on the system.
Table 6: Verbatim Text of INS Entry Exit System Expenditure Plan as Submitted to the Congress
Name Funding Spend plan
Description
CT Supplemental
$13,300,000
Entry Exit Support Contract $5,554,000 Entry Exit Support Contract—A contractor will assist the INS
in developing the Request for Proposal (RFP) for the Entry
Exit System. The contractor will also assist INS in evaluating
the proposals, developing the Concept of Operations and the
Business Case, and all requirements under Office of
Management and Budget Circular A-11, Part 7. The
contractor will also assist the INS in overseeing the design
and development of the Entry Exit System.
Interagency Agreement with the
National Institute for Standards and
Technology (NIST)
$1,000,000 Interagency Agreement (IAA) with the National Institute for
Standards and Technology (NIST)—This IAA requires NIST
to test biometrics and to assist the Attorney General and
Secretary of State to develop standards for biometrics
identifiers as required by the PATRIOT Act and the Enhanced
Border Security Act.
Interagency Agreement with the
White House Office of Science and
Technology (Biometrics)
$1,060,000 IAA with the White House Office of Science and
Technology—This IAA is to contract with a biometrics expert
to assist and advise the Entry Exit Office on possible
biometrics identifiers.
Travel $210,800
51
See, for example, U.S. General Accounting Office, Customs Service Modernization:
Third Expenditure Plan Meets Legislative Conditions, but Cost Estimating
Improvements Needed, GAO-02-908 (Washington, D.C.: Aug. 9, 2002) and Business Systems
Modernization: IRS Needs to Better Balance Management Capacity with Systems
Acquisition Workload, GAO-02-356 (Washington, D.C.: Feb. 28, 2002).

Page 31 GAO-03-563 Entry Exit System Expenditure Planning
Name Funding Spend plan
Description
CT Supplemental
$13,300,000
Facility Port Assessment $1,425,000 Port Facility Assessment—This is an assessment of the
current facilities present at every land border port along the
Canadian and Mexican borders.
Entry Exit Program Office Operations $159,000
Visa Waiver Permanent Program Act
(VWPPA) Task
$2,050,000 Visa Waiver Permanent Program At (VWPPA) Task—This is
the design, development and deployment of the system that
will record the arrival and departure of all Visa Waiver visitors
arriving and departing through air and sea ports-of-entry.
Interagency Agreement with U.S.
Customs Service (USCS)—(IBIS)
$560,000
Livescan Fingerprint Units $18,200
Entry/Exit System Prototyping $863,000 E/E System Prototyping—This is the prototyping of proposed
systems at various ports-of-entry that will culminate in the
award of a vendor to build the entry exit system.
Transportation Security
Administration (TSA) Prototype test
at Dulles International Airport (IAD)
$400,000 Transportation Security Administration (TSA) Prototype
Test—This is a joint TSA/USCS/Department of
State/INS/Department of Agriculture project with United
Airlines to develop an expedited process to inspect returning
US citizens.
Total $13,300,000 $13,300,000
The Entry Exit Program Manager states that to the best of his knowledge INS has complied with all acquisition rules, requirements,
guidelines, and system acquisition management practices of the Federal Government.
Source: INS.
The immense importance of the entry exit system to the security of our
nation’s borders is undeniable, as is the need to acquire and implement
this system effectively and efficiently. This criticality is a major reason that
the Congress placed limitations on the use of entry exit system funding
until the Congress has been assured, through the submission of a high-
quality plan, that the system is being managed effectively.
INS partially met the legislative conditions that the Congress placed on its
use of fiscal year 2002 entry exit system funding. However, it is important
that DHS promptly address certain capital planning and investment
control issues—security and privacy—and that the Congress be given the
opportunity to exercise its intended level of expenditure plan oversight
before funds are obligated. It is equally important that future expenditure
plans disclose sufficient information to permit meaningful congressional
understanding and oversight of the system. While this lack of detail is a
material limitation in the first plan, it will become even more problematic
in the future: as the magnitude and complexity of the entry exit system
acquisition increases in fiscal year 2003 and beyond, so will the
importance of creating plans with the appropriate level and scope of
information.
Conclusions

Page 32 GAO-03-563 Entry Exit System Expenditure Planning
Of particular significance going forward will be how effectively DHS
implements the system investment and acquisition controls provided for in
the first plan and related documentation. Therefore, it is important that
future plans disclose project information of sufficient level and scope
about (1) what system capabilities and benefits are to be delivered, by
when, and at what cost; (2) how well DHS is progressing against the
commitments that it made in prior expenditure plans; and (3) how the
acquisition is being managed to provide reasonable assurance that the
system capability, benefit, schedule, and cost commitments will be met.
This approach to expenditure planning for congressional oversight has
worked successfully with other federal agencies and the Congress.
To help ensure the effective management and acquisition of the entry exit
system, we recommend that the Secretary of Homeland Security, through
whatever entry exit program governance structure is established, direct
the entry exit program manager to ensure that planned investment and
acquisition management controls, including the development of a business
case, are fully implemented in accordance with recognized best practices
and relevant federal requirements and guidance. At a minimum, we
recommend that the Secretary’s direction include having the entry exit
program manager immediately develop and begin implementing a system
security plan. At the same time, we recommend that the Secretary have the
program manager perform a privacy impact analysis and use the results of
this analysis in near-term and subsequent system acquisition decision-
making. Further, in light of INS’s recent transition to the new department
and potential changes to system investment and acquisition controls
provided for in the first plan, we recommend that controls in the areas of
acquisition planning, solicitation, requirements management, project
management, contract tracking and oversight, and evaluation be
implemented in accordance with SEI guidance.
Additionally, we recommend that the Secretary ensure that future
expenditure plans (1) be provided to the department’s Senate and House
Appropriations Subcommittees in advance of entry exit system funds
being obligated and (2) fully disclose what entry exit system capabilities
and benefits are to be delivered, by when, and at what cost, and how it
intends to manage the acquisition to provide reasonable assurance that
these system capability, benefit, schedule, and cost commitments will be
met.
Recommendations for
Executive Action

Page 33 GAO-03-563 Entry Exit System Expenditure Planning
In written comments on a draft of our report signed by DHS’s Assistant
Secretary, Bureau of Immigration and Customs Enforcement (reprinted in
app. II, along with our responses), the department did not explicitly agree
or disagree with our conclusions and recommendations. However, the
department described actions that it plans to take that are consistent with
our recommendations, including developing and implementing a system
security plan, developing system management controls, providing future
expenditure plans to the Appropriations Subcommittees before obligating
any funds, and specifying system capabilities and benefits in future plans.
We support these planned actions.
The department provided other principal comments. First, it stated that we
failed to consider that the lack of specific detail in the fiscal year 2002
expenditure plan is attributable to a number of pending policy decisions.
Second, it stated that it had addressed the development of a system
security plan and privacy impact assessment and provided a draft
document entitled Technical Architecture and Security Requirements
that it said addressed these issues. Third, it commented that we concluded
that the entry exit program office is in compliance with INS’s ITIM, and
therefore the entry exit system is in compliance with OMB requirements.
Fourth, it said we failed to consider and incorporate information regarding
its obligation of supplemental appropriations.
We do not agree with these four comments. First, as we state in this
report, the legislative requirement to develop an expenditure plan is
intended to provide lawmakers with a sufficient understanding of the
system acquisition to permit effective oversight and informed decision-
making about the use of appropriated funds. For this to occur, the plan
needs to disclose a sufficient level and scope of information for the
Congress to understand what system capabilities and benefits are to be
delivered, by when, and at what cost. The plan also needs to disclose what
progress is being made against the commitments that were made in prior
expenditure plans, as well as how the acquisition will be managed to
provide reasonable assurance that system capability, benefit, schedule,
and cost commitments will be met. To the extent that this information was
not known because of pending policy issues, these issues should have
been explained and a timetable for addressing them included in the plan.
Notwithstanding these undecided policy matters, the plan could have
provided more detailed information. For example, it could have addressed
how the acquisition was to be managed.
Second, the draft document that the department provided with its
comments does not satisfy relevant federal guidance governing a security
Agency Comments
and Our Evaluation

Page 34 GAO-03-563 Entry Exit System Expenditure Planning
plan and a privacy impact assessment.
52
While the document acknowledges
the need to develop the plan and conduct the assessment, and the
document describes high-level security requirements, it does not include,
for example, rules of behavior for individuals who access the system and
the consequences for violating those rules; methods for identifying,
appropriately limiting, and controlling interconnections with other
systems; and procedures for periodically reviewing the effectiveness of
security controls. Similarly, the document does not include an assessment
of the privacy implications of personal information to be collected and
maintained by the system.
Third, while we state in this report that INS’s ITIM process generally
satisfies OMB’s requirement to establish a process that defines how the
agency selects, controls, and evaluates its IT projects, we do not state that
the program office is in full compliance with the ITIM process, and that
therefore the entry exit system is in compliance with OMB requirements.
Rather, we conclude that, in going forward, it is important that INS focus
on implementing the investment management controls provided for the
plan and related documentation. Accordingly, we recommend that DHS
fully implement planned investment management controls in accordance
with relevant federal requirements and guidance.
Fourth, we did not include in our draft report the information that the
department provided regarding its obligation of the supplemental
appropriations because the department provided this information to us in
a letter dated April 7, 2003. We sent our draft report to the department for
comment on April 3, 2003, before we received the department’s letter. We
have since modified this report, as appropriate, to incorporate the
information in the April 7, 2003, letter.
The department also provided additional technical comments, which we
have incorporated as appropriate into this report.
52
OMB Circular A-130, Revised (Transmittal Memorandum No. 4), Appendix III, “Security of
Federal Automated Information Resources” (Nov. 28, 2000); National Institute of Standards
and Technology, Guide for Developing Security Plans for Information Technology
Systems, NIST Special Publication 800-18 (December 1998); OMB Circular A-11, part 3,
Planning, Budgeting and Acquisition of Capital Assets (Washington, D.C.: July 2000).

Page 35 GAO-03-563 Entry Exit System Expenditure Planning
We are sending copies of this report to interested congressional
committees. We are also sending copies to the Secretary of Homeland
Security, the Director of the Office of Management and Budget, and the
Secretary of State. We will also send copies to others upon request. In
addition, copies will be available at no charge on our Web site at
www.gao.gov.
Should you or your offices have questions on matters discussed in this
report, please contact me at (202) 512-3439. I can also be reached by
E-mail at [email protected]. An additional GAO contact and staff
acknowledgments are listed in appendix V.
Randolph C. Hite
Director, Information Technology Architecture
and Systems Issues

Appendix I: Objectives, Scope, and
Methodology
Page 36 GAO-03-563 Entry Exit System Expenditure Planning
The Congress limited the ability of the Immigration and Naturalization
Service (INS) to obligate funds for the entry exit system until INS
submitted an expenditure plan (1) that meets the capital planning and
investment control review requirements established by the Office of
Management and Budget (OMB), including Circular A-11, part 3; (2) that
complies with the acquisition rules, requirements, and guidelines and
systems acquisition management practices of the federal government; and
(3) that is reviewed by us.
1
To satisfy our legislative mandate, our
objectives were to review INS’s expenditure plan to (1) determine whether
the plan satisfied the legislative conditions and (2) provide observations
about the expenditure plan and INS’s management of the entry exit
system. Our review focused not only on the plan, but also on related
system documentation and plans.
To determine whether INS’s expenditure plan satisfied the legislative
conditions, we first identified and analyzed relevant federal guidance, such
as OMB’s investment control review requirements and guidelines
2
and the
Federal Acquisition Regulation (FAR). We then reviewed INS’s
expenditure plan and related documentation, such as entry exit planning
documents (i.e., concept paper, concept of operations, business case, cost-
effectiveness study, and feasibility study); visa waiver support system
functional requirements, system design, and interface control documents;
and the concept of operations for the National Security Entry Exit
Registration System (NSEERS). We also interviewed the entry exit
program team program manager and other INS and Department of Justice
officials to determine what INS is doing to satisfy the legislative
conditions. To specifically address the legislative conditions, we did the
following:
• To determine whether INS’s expenditure plan met OMB’s capital planning
and investment control review requirements, we reviewed entry exit
planning documents and INS’s procedures for managing information
technology (IT) investments.
3
We then compared the planning documents
1
2002 Supplemental Appropriations Act for Further Recovery from and Response to
Terrorist Attacks on the United States, Public Law 107-206 (Aug. 2, 2002).
2
OMB Circular A-130, Management of Federal Information Resources (Washington, D.C.:
Nov. 28, 2000) and OMB Circular A-11, part 3, Planning, Budgeting, and Acquisition of
Capital Assets (Washington, D.C.: July 2000).
3
INS, Information Technology Investment Management Process and Procedure Guide,
Version 1.0 (December 2001).
Appendix I: Objectives, Scope, and
Methodology

Appendix I: Objectives, Scope, and
Methodology
Page 37 GAO-03-563 Entry Exit System Expenditure Planning
with OMB requirements to identify whether any variances existed. We
discussed reasons for variances with the entry exit program manager.
• To determine whether INS’s plan complies with federal acquisition rules,
requirements, and guidelines and systems acquisition management
practices, we reviewed INS’s policies and procedures for governing system
acquisition efforts, such as its System Development Life Cycle
4
and IT
investment management guidelines. We then identified and reviewed the
acquisition management best practices model
5
developed by the Software
Engineering Institute (SEI), which many federal agencies have adopted as
a benchmarking tool for acquiring software-intensive systems in a manner
that comports with federal acquisition rules, requirements, and guidelines.
Next, we compared the primary components of INS’s System Development
Life Cycle and its investment management procedures with the
components of SEI’s model to determine whether any variances existed.
The components addressed in SEI’s model were acquisition planning,
solicitation, requirements development and management, project
management, contract tracking and oversight, and evaluation. Because the
entry exit program manager stated that INS was following the
requirements of the FAR in acquiring the entry exit system, we also
compared selected sections of the FAR
6
(e.g., acquisition planning, and
contract negotiation and administration) with SEI’s model. Our
comparative analysis focused on whether key components of the SEI
model were provided for in the policies and procedures that INS was
following or intended to follow; it did not include evaluating the quality of
INS’s policies and procedures.
To identify observations about the expenditure plan and INS’s
management of the entry exit system, we first identified system
4
INS, Systems Development Life Cycle Manual, Version 6.0 (Apr. 5, 2002).
5
Carnegie Mellon Software Engineering Institute, Software Acquisition Capability
Maturity Model (SA-CMM
®
), Version 1.03 (March 2002).
6
Specifically, we reviewed Part 1 (Federal Acquisition Regulations System), Part 7
(Acquisition Planning), Part 11 (Describing Agency Needs), Part 15 (Contracting by
Negotiation), and Part 42 (Contract Administration and Audit Services).

Appendix I: Objectives, Scope, and
Methodology
Page 38 GAO-03-563 Entry Exit System Expenditure Planning
capabilities mandated in the applicable legislation.
7
Next, we identified
and reviewed the entry exit system’s planned operational requirements
and mapped the planned requirements to the legislatively mandated
system capabilities to identify any variances. We also compared INS’s
expenditure plan with those of two other agencies that have been required
to submit expenditure plans to the Congress (the Internal Revenue Service
and the U.S. Customs Service). We interviewed INS officials about plans
for providing information regarding the system’s benefits, schedules, and
costs in future expenditure plans.
The scope of our work was based on INS’s policies and procedures before
the transition to the Department of Homeland Security.
We conducted our work at INS headquarters in Washington, D.C., from
September 2002 through March 2003 in accordance with generally
accepted government auditing standards.
7
Section 110 of the Illegal Immigration Reform and Immigrant Responsibility Act of 1996,
Public Law 104-208 (Sept. 30, 1996); Immigration and Naturalization Service Data
Management Improvement Act of 2000, Public Law 106-215 (June 15, 2000); Visa Waiver
Permanent Program Act, Public Law 106-396 (Oct. 30, 2000); Uniting and Strengthening
America by Providing Appropriate Tools Required to Intercept and Obstruct Terrorism
(USA PATRIOT Act) Act of 2001, Public Law 107-56 (Oct. 26, 2001); Aviation and
Transportation Security Act, Public Law 107-71 (Nov. 19, 2001); and Enhanced Border
Security and Visa Entry Reform Act of 2002, Public Law 107-173 (May 14, 2002).

Appendix II: Comments from the Department
of Homeland Security
Page 39 GAO-03-563 Entry Exit System Expenditure Planning
Appendix II: Comments from the Department
of Homeland Security
Note: GAO comments
supplementing those in
the report text appear at
the end of this appendix.
See comment 1.

Appendix II: Comments from the Department
of Homeland Security
Page 40 GAO-03-563 Entry Exit System Expenditure Planning
See comment 3.
See comment 2.

Appendix II: Comments from the Department
of Homeland Security
Page 41 GAO-03-563 Entry Exit System Expenditure Planning
See comment 7.
See comment 6.
See comment 5.
See comment 4.

Appendix II: Comments from the Department
of Homeland Security
Page 42 GAO-03-563 Entry Exit System Expenditure Planning

Appendix II: Comments from the Department
of Homeland Security
Page 43 GAO-03-563 Entry Exit System Expenditure Planning
The following are GAO’s comments on the Department of Homeland
Security’s letter dated May 7, 2003.
1. We agree that the development of a system security plan and privacy
impact assessment of the system is a significant matter. We also
acknowledge that on May 6, 2003, the department provided us with a
draft document entitled Technical Architecture and Security
Requirements. However, we reviewed the document and found that it
does not include information consistent with a security plan and
privacy impact assessment. The Office of Management and Budget
(OMB) and the National Institute of Standards and Technology (NIST)
have issued security planning guidance.
1
In general, this guidance calls
for developing risk-based security plans that (1) provide an overview
of system security requirements, (2) describe the controls in place or
planned for meeting requirements, and (3) define responsibilities and
expected behavior for all individuals who access the system. The draft
document provided by the department acknowledges the need to
address but does not include many of these security plan elements,
such as rules of behavior for individuals who access the system and
the consequences for violating those rules; methods for identifying,
appropriately limiting, and controlling interconnections with other
systems; and procedures for periodically reviewing the effectiveness of
security controls. In addition, it does not, for example, describe the
specific controls in place or planned to address requirements or
delineate responsibilities and the expected behavior of individuals who
access the system. Similarly, the document does not include an
assessment of the privacy implications of personal information to be
collected and maintained by the entry exit system.
2. We disagree that we failed to consider that the lack of specific detail in
the fiscal year 2002 expenditure plan is attributable to a number of
policy decisions that are pending. As we state in this report, the
legislative requirement to develop an expenditure plan is intended to
provide lawmakers with a sufficient understanding of the system
acquisition to permit effective oversight and to allow for informed
decision-making about the use of appropriated funds. For this to
1
Office of Management and Budget Circular Number A-130, Revised (Transmittal
Memorandum No. 4), Appendix III, “Security of Federal Automated Information Resources”
(Nov. 28, 2000); National Institute of Standards and Technology, Guide for Developing
Security Plans for Information Technology Systems, NIST Special Publication 800-18
(December 1998).
GAO Comments

Appendix II: Comments from the Department
of Homeland Security
Page 44 GAO-03-563 Entry Exit System Expenditure Planning
occur, the plan needs to disclose a sufficient level and scope of
information for the Congress to understand what system capabilities
and benefits are to be delivered, by when, and at what cost, and what
progress is being made against the commitments that were made in
prior expenditure plans. Further, the plan should disclose how the
acquisition will be managed to provide reasonable assurance that
system capability, benefit, schedule, and cost commitments will be
met. Consequently, pending policy decisions that affect plans for the
entry exit program are precisely the kind of detail missing in this
expenditure plan that should be disclosed. To the extent that detailed
planning information is not known, this should be explained and a
timetable for obtaining this information included in the plan.
3. We agree that we concluded in this report that INS’s Information
Technology Investment Management (ITIM) process generally satisfies
OMB’s requirement to establish a process that defines how the agency
(1) selects projects included in its information technology portfolio;
(2) controls these projects to achieve the intended cost, schedule, and
performance outcomes; and (3) evaluates information technology
projects’ performance to maintain a positive return on investment. We
do not, however, state that the program office is in full compliance
with the ITIM process, and therefore the entry exit system is in
compliance with OMB requirements. Further, we concluded that of
particular significance going forward will be how effectively the
department implements the investment management controls provided
for its plan and related documentation. Accordingly, we recommended
that the department fully implement planned investment management
controls in accordance with relevant federal requirements and
guidance.
4. We have modified this report to recognize that an entry exit system
business case has yet to be developed, and we have added a
recommendation that the department develop a business case as part
of implementing planned investment management controls.
5. We do not question the department’s statement, because this was not
within the scope of our review.
6. We agree and have modified this report.
7. We sent our draft report to the department on April 3, 2003, which was
4 days before we received the department’s letter dated April 7, 2003.
We have since modified this report to reflect the information in the
April 7 letter.

Appendix III: Summary of Entry Exit Related
Systems
Page 45 GAO-03-563 Entry Exit System Expenditure Planning
Over the last year, INS has implemented two systems that are intended to
provide certain near-term border security capabilities until the entry exit
system is acquired and implemented. These two systems are the Visa
Waiver Permanent Program Act Support System and the National Security
Entry Exit Registration System (NSEERS). According to the entry exit
program manager, both systems will be integrated into the entry exit
system.
On October 1, 2002, INS implemented the Visa Waiver Permanent Program
Act Support System. This system electronically collects arrival and
departure information for all passengers and crew members who are
provided a waiver and who arrive and depart U.S. airports and seaports. It
modifies two existing systems—Customs’ Advance Passenger Information
System (APIS) and INS’s Arrival Departure Information System (ADIS)
1
—
in collecting information.
• Arrival: Before entering an air or sea port of entry, commercial carriers
must electronically submit manifest information (e.g., for each passenger
and crew member, the person’s name, address, country of residence, and
passport number) to APIS. This information is queried against several
databases, including the Interagency Border Inspection System (IBIS)
Consolidated Lookout Database and the Datashare Immigrant Visa
database.
2
Receiving the manifest data before carriers arrive allows INS to
review the data beforehand and identify passengers who will require
referral to secondary inspection. The inspector also inputs the “Admit
Until” date into IBIS, which establishes the foreign national’s length of
stay. Both the manifest data and the approved length of stay are
transmitted to ADIS.
• Departure: Carriers are also required to electronically submit to APIS
manifest information of passengers leaving the United States from an air
or sea port. The departure manifest information is transmitted from APIS
1
The ADIS system was originally developed as part of the Automated Form I-94 system. The
Automated Form I-94 system was developed to electronically collect Form I-94 arrival and
departure data. However, INS determined that the electronic system was not meeting its
mission needs and retired the system in February 2002. The Form I-94 data continue to be
collected manually.
2
Through the DataShare Program, information on nonimmigrant visa applications is passed
electronically between the Department of State and INS. The National Visa Center receives
INS petition data electronically and, in turn, electronically transfers cases to U.S.
embassies and consulates.
Appendix III: Summary of Entry Exit Related
Systems
Visa Waiver
Permanent Program
Act Support System

Appendix III: Summary of Entry Exit Related
Systems
Page 46 GAO-03-563 Entry Exit System Expenditure Planning
to ADIS, which uses name-matching algorithms to match the arrival and
departure records. The matching results are used to identify persons who
have overstayed their authorized visits.
According to the entry exit program manager, INS has been able to match
98 percent of received departure records to arrival records. The program
manager also estimated that there are currently 16 million outstanding
(i.e., unmatched) arrival records. He also estimated that INS receives
about 350,000 arrival records per day.
On June 5, 2002, the Attorney General established the NSEERS program to
capture information about certain foreign nationals entering, staying in,
and exiting the United States. In brief, NSEERS consists of (1) a modified
version of an existing INS system used to collect and record enforcement
data, the Enforcement Case Tracking System;
3
(2) more deployments of an
existing INS biometric capture/analysis system, the Automated Biometric
Identification System;
4
and (3) updated business processes/rules covering
the registration of certain nonimmigrants.
5
Under the updated business
processes/rules, existing registration requirements
6
were changed to
require certain nonimmigrant aliens to report to INS upon arrival;
approximately 30 days after arrival; every 12 months after arrival; upon
certain events (e.g., change of address, employment, or school); and at the
3
The Enforcement Case Tracking System is a case management system, which supports
INS’s apprehension and booking process for illegal aliens. Capabilities include interfacing
with systems external to INS (e.g., Customs Service inspection lookout systems, state
prison information systems, and State Department information systems).
4
The Automated Biometric Identification System is an INS database of more than 4.5
million foreign visitors’ fingerprints. The system includes a two-print biometric
identification functionality that collects fingerprints and photos.
5
8 CFR 214.1(f) and 264.1(f), published in the Federal Register, Volume 67, No. 155 (Aug.
12, 2002)—Registration and monitoring of certain nonimmigrants, which include nationals
from Iran, Iraq, Libya, and Sudan. Justice has subsequently identified other countries to be
subject to the special registration requirements; making these identifications is now the
responsibility of the Department of Homeland Security. As of March 2003, the department
reported that 25 countries are subject to these special registration requirements.
6
Section 263 of the Immigration and Nationality Act (ch. 477,66 stat. 163, 224 (1952))
authorizes the Attorney General, at his discretion, to prescribe special registration
requirements for certain nonimmigrants admitted to the United States. Existing regulations
require INS to register nonimmigrants using Form I-94 (Arrival-Departure Record), but
contain general provisions waiving the fingerprinting requirement for many nonimmigrants
(8 CFR 264.1(e)). Section 262 of the act gives the Attorney General additional general
registration authority.
National Security
Entry Exit
Registration System

Appendix III: Summary of Entry Exit Related
Systems
Page 47 GAO-03-563 Entry Exit System Expenditure Planning
time of departure from the United States. Registration requirements also
now include photographing and fingerprinting the alien and matching both
against criminal and terrorist watch lists. According to INS, NSEERS was
deployed to a limited number of sites on September 11, 2002, and became
fully operational at 238 INS locations on October 1, 2002.

Appendix IV: Summary of Legislation
Regarding Entry Exit System Capabilities
Page 48 GAO-03-563 Entry Exit System Expenditure Planning
Legislation Provisions
Illegal Immigration Reform and Immigrant
Responsibility Act of 1996
Public Law 104-208
September 30, 1996
By September 30, 1998, the Attorney General shall develop an automated entry exit
control system that—
(1) collects a record of departure for every alien departing the United States and matches
it with the corresponding arrival record and
(2) identifies, through on-line searching procedures, lawfully admitted aliens who overstay
their visas.
Overstay information identified through the system shall be integrated into appropriate
databases of the Immigration and Naturalization Service (INS) and the Department of
State, including those used at ports of entry and at consular offices.
Notwithstanding any other provision of federal, state, or local law, a federal, state, or local
government entity or official may not prohibit or in any way restrict any government entity
or official from sending to or receiving from INS information regarding the citizenship or
immigration status, lawful or unlawful, of any individual.
INS Data Management Improvement Act
of 2000
Public Law 106-215
June 15, 2000
For the purposes of this section, the term “integrated entry and exit data system” means
an electronic system that—
(1) provides access to, and integrates, alien arrival and departure data that are
(a) authorized or required to be created or collected under law; (b) in an electronic format;
and (c) in a database of the Department of Justice or the Department of State, including
those created or used at ports of entry and at consular offices;
(2) uses available data described above to produce a report of arriving and departing
aliens by country of nationality, classification as an immigrant or nonimmigrant, and date
of arrival in and departure from the United States;
(3) matches an alien’s available arrival data with the alien’s available departure data;
(4) identifies, through on-line searching procedures, lawfully admitted nonimmigrants who
may have remained in the United States beyond the period authorized by the Attorney
General; and
(5) otherwise uses available alien arrival and departure data described in paragraph (1)
above to permit the Attorney General to make the reports required under 8 U.S.C. section
1365a(e):
• Number of departure records collected, with an accounting by nationality.
• Number of departure records that were successfully matched to records of arrival, with
an accounting by nationality and classification as an immigrant or nonimmigrant.
• Number of aliens who arrived pursuant to a nonimmigrant visa, or the Visa Waiver
Program, for whom no matching departure data have been obtained through the
system or by other means as of the end of the alien’s authorized period of stay, with an
accounting by nationality and arrival date in the United States.
• Number of lawfully admitted nonimmigrants identified as visa overstays, with an
accounting by nationality.
The Attorney General shall implement the integrated entry exit system at airports and
seaports by December 31, 2003. System requirements:
• include available arrival/departure data,
• ensure that the arrival/departure data, when collected or created by an immigration
officer, are entered into the system and can be accessed by other officers at other
air/seaports.
The Attorney General must implement the system at the 50 busiest land border ports of
entry by December 31, 2004. System requirements:
• Same as specified above
• Arrival/departure data on aliens shall be accessible at other high-traffic land border
ports of entry.
The system shall be fully implemented at all remaining ports of entry by December 31,
2005.
Appendix IV: Summary of Legislation
Regarding Entry Exit System Capabilities

Appendix IV: Summary of Legislation
Regarding Entry Exit System Capabilities
Page 49 GAO-03-563 Entry Exit System Expenditure Planning
Legislation Provisions
Visa Waiver Permanent Program Act
Public Law 106-396
October 30, 2000
Not later than October 1, 2001, the Attorney General shall develop and implement a fully
automated entry exit control system that will collect a record of arrival and departure for
every alien who arrives and departs by sea or air at a port of entry in the United States
and is provided a waiver.
Not later than October 1, 2002, the system shall enable immigration officers conducting
inspections at ports of entry to obtain from the system, with respect to aliens seeking a
waiver, (1) any photograph of the alien that may be contained in the records of the State
Department or INS; and (2) information on whether the alien has ever been determined to
be ineligible to receive a visa or be admitted to the United States.
The system shall maintain, for a minimum of 10 years, information about each application
for admission made by an alien seeking a waiver.
On and after October 1, 2007, the alien at the time of application for admission must have
a valid unexpired machine-readable passport that satisfies the internationally accepted
standard for machine readability.
Countries designated to participate before May 1, 2000, shall issue machine-readable
passports no later than October 1, 2003.
All Visa Waiver Program (VWP) applicants are to be checked against lookout systems.
By October 1, 2002, no waiver may be provided to an alien arriving by air or sea at a port
of entry on a carrier unless the carrier is electronically transmitting passenger data to the
entry exit system.
Not less than 1 hour before arrival at port of entry, signatory aircraft transporting VWP
aliens must electronically furnish the passenger data required by the Attorney General in
regulations.
The system shall contain sufficient data to permit the Attorney General to calculate, for
each program country and each fiscal year, the portion of nationals of that country who
arrive under VWP at air and sea ports of entry but for whom no record of departure exists,
expressed as a percentage of the total number of such VWP aliens for the particular
country.
USA PATRIOT Act
Public Law 107-56
October 26, 2001
Focus of system development shall be on (a) utilization of biometric technology and
(b) tamper-resistant documents readable at ports of entry.
The system must be accessible to (a) all consular officers responsible for visa issuance,
(b) all federal inspection agents at all U.S. border inspection points, and (c) all law
enforcement and intelligence responsible for investigation or identification of aliens.
The entry exit system must be able to interface with law enforcement databases to be
used by federal law enforcement to identify and detain individuals who pose a threat to
the national security of the United States.
Aviation and Transportation Security Act
Public Law 107-71
November 19, 2001
(1) Not later than 60 days after the date of enactment, each air carrier and foreign air
carrier operating a passenger flight in foreign air transportation to the United States shall
provide to the Commissioner of Customs by electronic transmission a passenger and
crew manifest containing the following information:
• The full name of each passenger and crew member.
• The date of birth and citizenship of each passenger and crew member.
• The sex of each passenger and crew member.
• The passport number and country of issuance of each passenger and crew member if
required for travel.
• The U.S. visa number or resident alien card number of each passenger and crew
member, as applicable.
• Such other information as the Under Secretary of Transportation for Security, in
consultation with the Commissioner of Customs, determines is reasonably necessary
to ensure aviation safety.
Carriers may use the advanced passenger information system established under section
431 of the Tariff Act of 1930 (19 U.S.C. 1431) to provide the information required by the
preceding sentence.

Appendix IV: Summary of Legislation
Regarding Entry Exit System Capabilities
Page 50 GAO-03-563 Entry Exit System Expenditure Planning
Legislation Provisions
(2) Passenger name records—The carriers shall make passenger name record
information available to the Customs Service upon request.
(3) Transmission of manifest—a passenger and crew manifest required for a flight under
paragraph (1) above shall be transmitted to the Customs Service in advance of the
aircraft landing in the United States in such manner, time, and form as the Customs
Service prescribes.
(4) Transmission of manifests to other federal agencies—Upon request, information
provided to the Under Secretary or the Customs Service under this subsection may be
shared with other federal agencies for the purpose of protecting national security.
Enhanced Border Security and Visa
Entry Reform Act of 2002
Public Law 107-173
May 14, 2002
No later than October 26, 2004, the Secretary of State and the Attorney General shall
issue to aliens only machine-readable, tamper-resistant visas and other travel and entry
documents that use biometrics.
In addition to the requirement for biometric identifiers, name-search capacity and support
must also be implemented between 18 months and 4.5 years after the date of enactment.
Not later than October 26, 2004, the Attorney General and Secretary of State shall install
at all U.S. ports of entry equipment and software to allow biometric comparison and
authentication of all U.S. visas and other travel and entry documents issued to aliens.
Not later than January 1, 2003, arrival and departure manifests must be electronically
provided to appropriate immigration officers for each passenger (including crew members
and any other occupants) of air and sea carriers at port of entry.
The information to be provided with respect to each person listed on a manifest shall
include (1) complete name; (2) date of birth; (3) citizenship; (4) sex; (5) passport number
and country of issuance; (6) country of residence; (7) U.S. visa number, date, and place
of issuance, where applicable; (8) alien registration number, where applicable; (9) U.S.
address while in the United States; and (10) such other information that the Attorney
General, in consultation with the Secretaries of State and the Treasury, determines as
being necessary for the identification of the persons transported and for the enforcement
of the immigration laws and to protect safety and national security.
Sources: Cited legislation.

Appendix V: GAO Contacts and Staff
Acknowledgments
Page 51 GAO-03-563 Entry Exit System Expenditure Planning
Deborah Davis, (202) 512-6261
In addition to the person named above, other key contributors were Carol
Cha, Barbara Collier, Neil Doherty, Ashfaq Huda, Richard Hung, Franklin
Jackson, Tammi Nguyen, and Jamelyn Smith.
Appendix V: GAO Contacts and Staff
Acknowledgments
GAO Contact
Staff
Acknowledgments
(310245)

The General Accounting Office, the audit, evaluation and investigative arm of
Congress, exists to support Congress in meeting its constitutional responsibilities
and to help improve the performance and accountability of the federal
government for the American people. GAO examines the use of public funds;
evaluates federal programs and policies; and provides analyses,
recommendations, and other assistance to help Congress make informed
oversight, policy, and funding decisions. GAO’s commitment to good government
is reflected in its core values of accountability, integrity, and reliability.
The fastest and easiest way to obtain copies of GAO documents at no cost is
through the Internet. GAO’s Web site (www.gao.gov) contains abstracts and full-
text files of current reports and testimony and an expanding archive of older
products. The Web site features a search engine to help you locate documents
using key words and phrases. You can print these documents in their entirety,
including charts and other graphics.
Each day, GAO issues a list of newly released reports, testimony, and
correspondence. GAO posts this list, known as “Today’s Reports,” on its Web site
daily. The list contains links to the full-text document files. To have GAO e-mail
this list to you every afternoon, go to www.gao.gov and select “Subscribe to daily
E-mail alert for newly released products” under the GAO Reports heading.
The first copy of each printed report is free. Additional copies are $2 each. A
check or money order should be made out to the Superintendent of Documents.
GAO also accepts VISA and Mastercard. Orders for 100 or more copies mailed to a
single address are discounted 25 percent. Orders should be sent to:
U.S. General Accounting Office
441 G Street NW, Room LM
Washington, D.C. 20548
To order by Phone: Voice: (202) 512-6000
TDD: (202) 512-2537
Fax: (202) 512-6061
Contact:
Web site: www.gao.gov/fraudnet/fraudnet.htm
E-mail: fraudnet@gao.gov
Automated answering system: (800) 424-5454 or (202) 512-7470
Jeff Nelligan, Managing Director, [email protected]v (202) 512-4800
U.S. General Accounting Office, 441 G Street NW, Room 7149
Washington, D.C. 20548
GAO’s Mission
Obtaining Copies of
GAO Reports and
Testimony
Order by Mail or Phone
To Report Fraud,
Waste, and Abuse in
Federal Programs
Public Affairs
